This article is more than 1 year old
How to upgrade an Acer Aspire One netbook's memory
Screwdriver at the ready
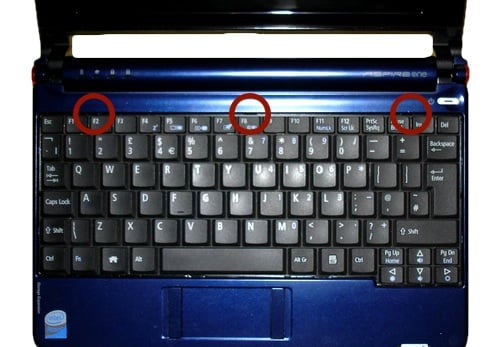
5. Turn the AA1 over and open the lid. You need to remove the keyboard next. It's held in place with three spring-loaded clips, marked below. Using the screwdriver, gently press each one in and it'll release the keyboard. You have to push hard, but be careful not to slip and scratch your AA1. You can use the corner of a credit card instead, which should minimise the risk of scratching, but makes it harder to push in the clips.
As each clip gets pushed in, it should raise the keyboard enough to get either the flat-blade screwdriver or card in to hold it open - albeit only a tiny amount.
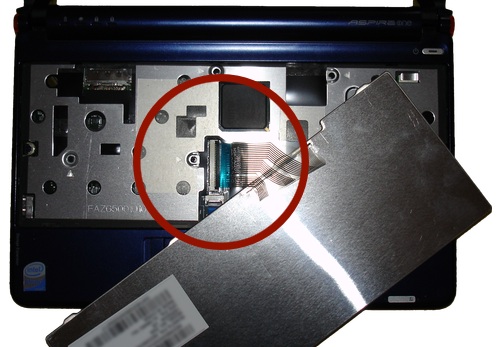
Once it's free at the back, lift the keyboard gently forward and two side clips will come free allowing you to remove it. Take care not to yank it off - there's a cable underneath you need to remove first.
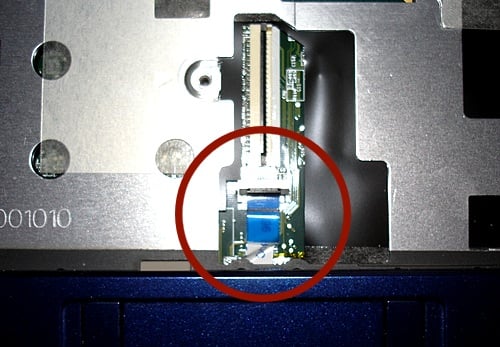
6. The keyboard cable's attached to the AA1 with a simple clip: just flip up the black clip with your fingernail and you'll be able to slide the keyboard cable out.
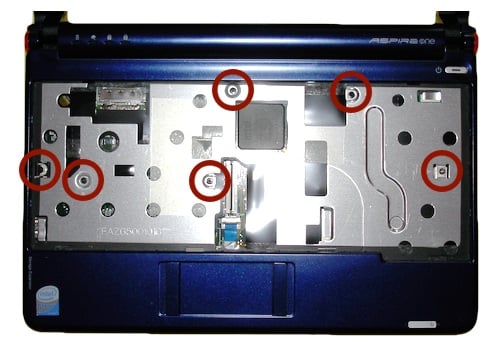
7. Remove the marked screws.
8. Below the keyboard connector, you'll see a similar but smaller attachment for the trackpad cable. Again, flip up the black catch to release the cable.