This article is more than 1 year old
How to upgrade an Acer Aspire One netbook's memory
Screwdriver at the ready
Acer's Aspire One A110/A150 may have been knocked off the top of the totem pole by Samsung's NC10, and it may be on the verge of being superseded by its new big brother, the 10in version, but it's proved a hugely popular netbook.
Lots of folk own one, lots of folk use one and lots of folk reckon the base model doesn't have enough memory.
The bundled Linux distro, Linpus, will work happily in 512MB, but if you want to replace it with a more capable, less limited version of the open source OS, we'd say upping the memory to 1GB isn't a bad idea, not least given how inexpensive extra Ram is these days. If it's Windows you prefer, you probably want to go the whole hog and take the memory complement to 1.5GB, the maximum the machine can cope with.
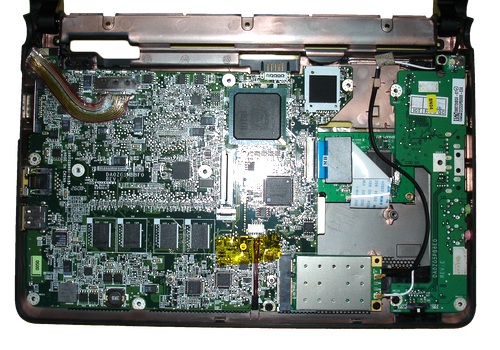
Inside the Acer Aspire One
But, unlike some other netbooks, the Aspire One hasn't been designed with easy upgrading in mind. The first 512MB is soldered to the motherboard, but there is a DIMM slot for more, and it's facing the base of the machine. The only snag: Acer's engineers didn't put a hatch above it to make the slot easily reachable.
Instead, you have to disassemble the machine and remove the motherboard. That may sound a daunting task, and we'd not recommend it for everyone, but it's not hard to do. What follows, then, is our step-by-step guide.
First, though, the obligatory cautionary note: taking your AA1 - or someone else's - to bits will invalidate your warranty, make it easier for you to kill the machine and might turn your hair quite white. Proceed at your own risk. Get it wrong and you'll have no recourse here. You have been warned.
You'll also need the following tools: a small-blade philips screwdriver, a small-blade flat screwdriver and a credit card.
1. Turn the AA1 off and disconnect it. Lay it lid down. We always do this on a sheet to minimise the risk of scratching the case, and to help avoid losing screws - they're less likely to roll of the table. We also recommend placing the removed screws in pattern that matches the holes they'll go back into.
2. Remove the following screws.

3. Take off the battery and remove the three marked screws.

Nb. Yes, we know this shot shows two previously removed screws still in place. The photographer's been sent to the Moderatrix for discipline...
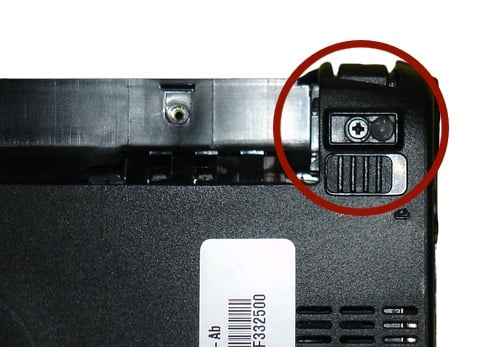
4. Two further screws are hidden by the AA1's rear rubber feet. The feet are held in place with a light adhesive and can be easily (gently does it) prized of with a flat-blade screwdriver. The remove the screw beneath each foot.