This article is more than 1 year old
Sony shows off stacks more compact cameras
And a rather nice 'superzoom'
Sony has introduced a bevvy of Cyber-shot compact cameras, some skinny, others chunkier, but all with double-digit megapixel counts.
The slimline line-up comprises the T900 and the lesser T90. The extra '0' means the T900 has a 3.5in LCD rather than a 3in one, but both cameras have a 12.1Mp sensor, 4x optical zoom, 720p HD movie shooting capacity, and smile- and face-detection technology.

Sony's Cyber-shot T900: slimline
Curiously, the T900's slightly thicker than the T90: 15.1mm to 13.9mm, but what's 1.2mm among chums?
The 12.1Mp W290 and W270 are thicker still, but pack in a 28mm 5x optical zoom with 28mm wide-angle lens. They too do 720p movies, and provide face- and smile-detection and technology. They have optical image stabilistation too.

The W230: no 720p recording - unlike its W-series siblings
A lesser model, the W230, makes do with a 30mm lens, 4x optical zoom and lacks 720p recording.
The low-end S980 has a 4x zoom, the even-lower-end S930 a 3x zoom. The pair have 12.1 and 10.1 megapixels, respectively, digital image stabilisation and face detection.
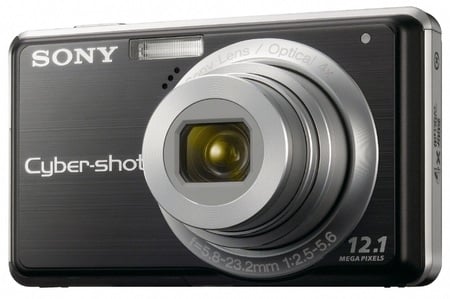
The S980: basic
If these two cameras - and the other ones, for that matter - are too low end for you, Sony also unveiled the H20, a bridge-style boy decked out in black and sporting a 10.1Mp sensor, 10x optical zoom and the 720p, smile and face recognition, and optical stabilisation features of its siblings.

The H20:
Sony kept mum about pricing, but it did say the S980 will go on sale at the end of the month. The W290 and W270 will be available from mid-March, the T900 and T90 from the end of March, the the W230 and S930 from mid-April and the H20 from the end of that month. ®

10x optical zoom
