This article is more than 1 year old
Western Digital My Book World Edition 1TB NAS box
Great value network storage
We plugged the My Book into an Apple Time Capsule 802.11n router to which we also connected the Ethernet port of a MacBook Pro to the Time Capsule, ensuring a Gigabit pathway from My Book to router to Mac.
Single 8GB File Copy Results
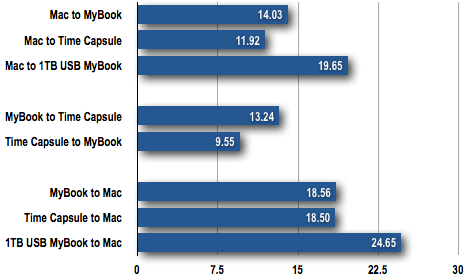
Bandwidth in Megabytes per Second (MB/s)
Longer bars are better
The Time Capsule contains a 500GB 7200rpm Enterprise-class Seagate drive. That's half the capacity of the drive in the My Book, but it pumped out consistently more heat during testing - though it's worth bearing in mind that the TC's AC adaptor is built in; the My Book's is separate. That said, the Apple unit is more tightly sealed, so there was little to choose between them when it came to noise, with not much of it.
First, we copied an 8GB file from MacBook Pro to the two drives, between the drives and then back to the laptop. The My Book's drive is nominally rated at 7200rpm, but you can see from the chart that we got better file copy performance from the WD than from the Apple unit.
We should point out that we made sure the Time Capsule's drive was spinning before timing the copy actions. The Time Capsule's firmware spins down the HDD after a period of inactivity, partly to conserve power, but mostly to help keep the heat down. Add in the TC's drive spin-up time, an the My Book's lead is enhanced. And it was always ready to begin copying files immediately.
Single 14.67GB Folder Copy Results
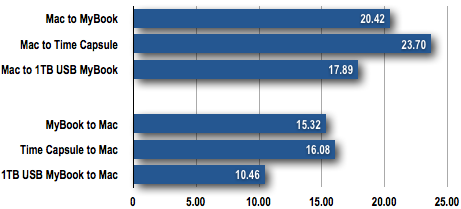
Time in Minuts
Shorter bars are better
Still, it's not quite the equivalent of hanging a USB drive off a single machine, and we've included appropriate figures to show you. Maybe with a fast desktop drive, you'd get close to USB speeds, but not with your average laptop. And certainly not if you're connecting your computer to the router over Wi-Fi or 10/100Mb/s Ethernet.
