This article is more than 1 year old
Users: The weakest link in laptop security
Is end user training still an optional luxury?
Reg Tech Panel If you ask the average business person who is responsible for the security of data held in computer systems, the chances are they will point to the IT department. After all, it's all about passwords, keys, firewalls, locks on computer room doors and other systems-related perceptions they have picked up without ever really having thought about it.
OK, we might be doing some business people a disservice here, but when a breach occurs, it's never very long before IT's phone starts to ring.
At the same time, it never ceases to amaze IT people, particularly those in support, how irresponsible some users can be. No one reading this needs a lesson in the risks that irresponsible or thoughtless user behaviour represents, but when it comes to laptop usage, it focuses the mind to see some of the common exposures listed together:
- Leaving equipment unattended, on view and wide open to theft in cars, coffee shops and other public places.
- Bringing sensitive information up on screen for anyone in close proximity to read when sitting on the plane, train, etc.
- Having everything set up to automatically log in to systems and websites with usernames and passwords saved locally. Break into the machine, and you're into everything else.
- Letting someone else 'borrow' their laptop to get online for a few minutes to check their email.
- Letting the kids play on their PC, load dubious software from dubious sources, and access dodgy sites on the internet.
- Loading dubious software from dubious sources, and accessing dodgy sites on the internet themselves!
- Disabling or working around security measures implemented by IT because they're inconvenient and slow things down.
- Connecting to any wireless network available without any thought about who owns it and who else might be on it.
These are just examples, and I am sure you can think of more.
The obvious one we haven't mentioned is the minefield created by the ease with which information can be copied and exchanged via removable media such as USB keys. Mobile users with laptops are particularly prone to exposure here, as they typically interact routinely with more external people with whom they are likely to want to share information. Apart from the risk of sensitive data ending up in wrong hands, there is always the chance of picking up malware from others’ devices that the user plugs into their own machine.
The reality is that the weakest link when it comes to mobile security is the user, not the technology. So how do we deal with this?
Well, putting some policies, procedures and guidelines in place is an obvious place to start if they don't exist already. However, Reg research conducted a while back (pdf) in relation to mobile working in general suggests that this itself isn't enough.
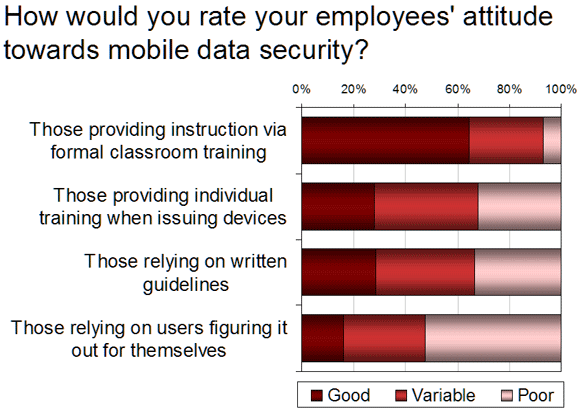
The feedback we received showed a strong correlation between the proactive training of users and their attitude and awareness with regard to security. Organisations who implemented formal classroom based training in particular stood out as having a much higher degree of confidence in their workforce:
With this in mind, we are interested in your experiences of dealing with the 'human factor' when it comes to laptop security. Examples of less than intelligent behaviour, views of the most common areas of exposure that exist and, in particular, experiences from things you have tried or implemented that have worked or otherwise would be interesting to hear.
If you have any thoughts about where the buck stops on this issue - with IT, HR, business managers or even users - then your feedback on that question would be interesting too. So, let us know what you think in the comments below. ®
