This article is more than 1 year old
Apple iPhoto gets in your face
You look great. It's getting old
Getting in your face
The ease of importing photos into iPhoto depends upon where they're coming from.
The simplest way is to drag a folder full of photos out of a Finder window, then drop it into iPhoto's main workspace. The folder will be added as an Event, which is iPhoto's way of automatically grouping photos. If you drag a folder that contains nested folders, each will be added as its own event. Each Event will be named with the folder's name.
It doesn't matter what Library you're in when you drag-and-drop to import photos. iPhoto will automatically switch into import mode.
You can also upload photos directly from your digital camera. If that camera stores its images in memory - either a removable card or, as with the iPhone, internal memory - iPhoto will display all the photos before import and ask which you want to import.
Once your first photos are imported, you can begin using one of iPhoto '09's most-ballyhooed features, the face-recognition system called Faces.
To begin using Faces, click the Faces icon in the Library list to the left of the main workspace. You'll be greeted with a brief set of instructions (below) on how to get Faces up and running.
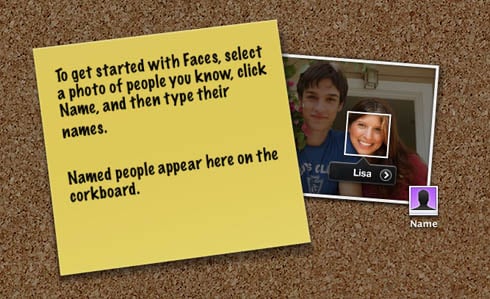
Once you first use Faces, you'll never see this cheery note again
After you select and name your first Face, it will appear as a named thumbnail on the corkboard background of the Faces workspace. The next time you import photos, iPhoto will scan them for matching faces, and add the matches to the Faces group for that individual.
We discovered that although Faces seems to be remarkably dunderheaded at first, it can be taught to recognize faces rather quickly and efficiently. Click on a Faces thumbnail on the corkboard, and iPhoto will display the photos you have identified, and below them photos that it thinks are of the same person. You then click the Confirm Name icon in the bottom toolbar, then single-click the photos that are correct and double-click the ones that aren't.
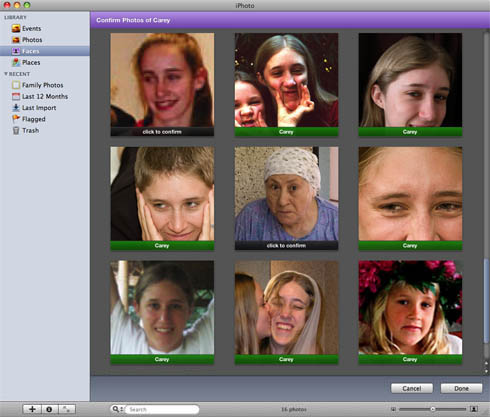
Before training, Faces mistook an all-American girl for a 70-year-old Turkish peasant
Our first iteration or two of this training regimen were disappointing, with results well under 10 per cent correct in most cases. Early results could also be alternately comical and intriguing - you may be discomfited, as was true in our case, when Faces mistakes you for Bill Gates.
As we iterated the Confirm Name sequence two or three more times, we discovered Faces to be clearly influenced by family resemblances, routinely grouping family members out of our hundreds of test photos.
After a half-dozen or so iterations, Faces smartened up. After that amount of training, it did a surprisingly good job of selecting photos taken over a wide range of a person's years, even when those photos were scans of less-than-sharp, aging snapshots.
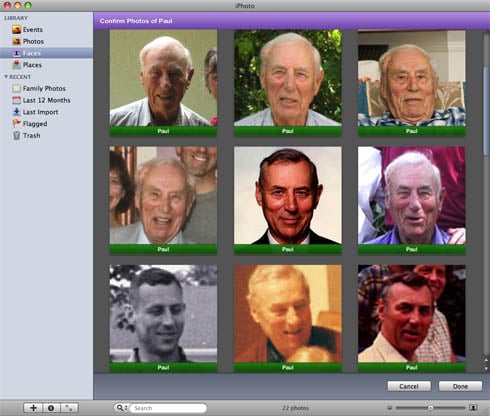
Faces found photos of Paul throughout his 92 years
Even after a good amount of training, however, Faces still had trouble with sunglasses and photos of folks looking off to the side - although we did discover that if an individual wears the same pair of sunglasses in a large amount of photos, Faces will eventually catch on.
Faces doesn't actually move any photos from their individual Events in the iPhoto Library. Instead, it works like iPhoto's familiar Smart Albums and creates pointers to them - pointers that assemble all photos of a Faces-identified person into his or her named group.
The same Smart-Album mimicking is performed by iPhoto '09's other major new feature, Places.
