This article is more than 1 year old
Google mistakes entire web for malware
This internet may harm your computer
Updated A human error at Google caused its main search engine to briefly identify every site on the web as a potentially malicious destination that represented a threat to end users, the company said.
Starting early Saturday morning California time, the world's largest search engine flagged each search result with the warning: "This site may harm your computer".
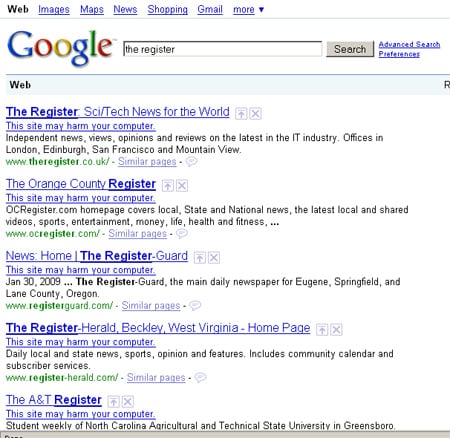
Google: internet bad
Attempts to visit a search link were met with Google's standard malware warning, which blocks users from actually reaching the intended destination:
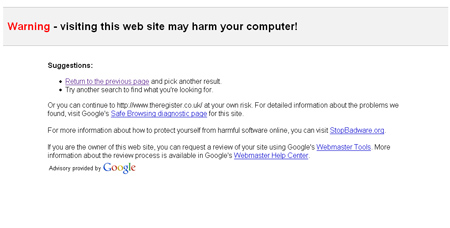
Do not proceed to internet
The glitch lasted for about an hour.
A post left a few hours later on a Google blog blamed the glitch on "human error." It seems someone in Mountain View mistakenly designated a "/" as a site that was surreptitiously trying to install malware on visitors' machines. Google's malware warning system took that to mean that every site on the internet was potential harmful to its users.
"Fortunately, our on-call site reliability team found the problem quickly and reverted the file," Marissa Mayer, Google's VP of search products and user experience, wrote. "Since we push these updates in a staggered and rolling fashion, the errors began appearing between 6:27 a.m. and 6:40 a.m. and began disappearing between 7:10 and 7:25 a.m., so the duration of the problem for any particular user was approximately 40 minutes."
Google's malware warning system is a joint effort between the search giant and StopBadware.org. Together, they generate a list in real time of sites believed to sneak malware and unwanted software onto visitors' machines. ®
