This article is more than 1 year old
Sony Ericsson cameraphone spied online
Pretty as a peach
A Sony Ericsson surprise announcement planned for Mobile World Congress (MWC) next month may have been rumbled, because pictures of one of the firm’s upcoming cameraphones has been leaked online.
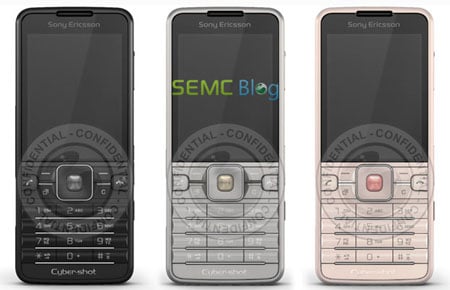
Sony Ericsson's C901
Thought to be codenamed 'Filippa' and officially called the Cyber-shot C901, various online sources have speculated that the phone has a 5Mp camera on board and the increasingly common smile-recognition feature.
Autofocus and a senon flash – for perfectly illuminated photos – are also thought to feature on the phone.
None of the phone’s connectivity features have been leaked yet.
For the fashion conscious, you’ll be pleased to know that the pictured models each have matching names: “Noble Black”, “Sincere Silver” and... ahem... “Precious Peach”.
We hope to bring you some official news about the C901 from MWC next month. ®
