This article is more than 1 year old
Desktop integrated graphics shoot-out
The best IGPs from Intel, AMD and Nvidia slug it out
We compared three Intel motherboards using a Core 2 Duo E8500 that runs at 3.16GHz at a cost of £150, while the two AMD chipsets were run on an Athlon X2 7750 that, at £65, is considerably cheaper. Both processors are dual core and, despite the name, the Athlon X2 7750 is actually a two-core Phenom so the memory support runs to 1066MHz DDR 2. The Intel motherboards also support DDR 2 rather than DDR 3.
The Athlon X2 7750 has a clock speed of 2.7GHz so we raised the speed to 2.8GHz on standard voltages to give it slightly more grunt without increasing the power draw or heat output.
3DMark06 Results
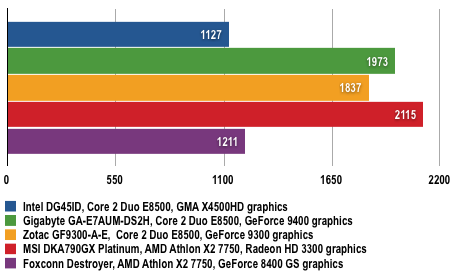
Longer bars are better
Power Draw Results
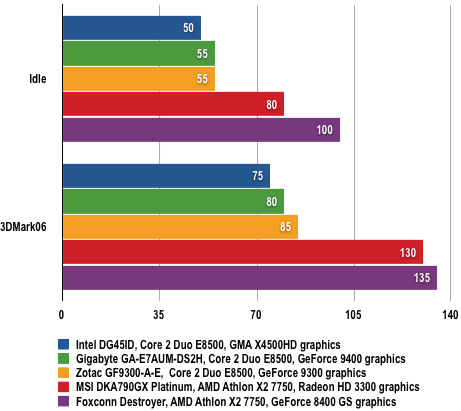
Power draw in Watts (W)
