This article is more than 1 year old
Toshiba NB100 netbook
Tosh takes netbooks seriously - too seriously...
Review There are netbooks that have a curvy, kid-friendly look. Others are sleek and shiny - every one aimed at adults. Then there are blocky, serious looking ones, carved with no concession to consumer levity and fluff because the manufacturer reckons that's what businesspeople want.
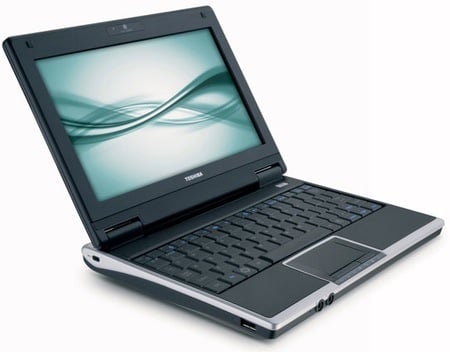
Toshiba's NB100: boxy, 'serious' design
The box-like Toshiba NB100 falls squarely - in both senses of the word - into the latter camp. There's a nod to designeriness: the silvery-bronze "champagne gold" plastic that edges around the main body of the machine curves at the sides, but that's it's only concession to modern styling and other such frippery.
The lid is likewise covered in silver-bronze look plastic - though glossy this time - and the rest of the NB100 is matte black. The lid is hinged slightly forward from the back and pivots on two raised, solid hinge units which also gives the NB100 a vaguely retro look too.
There's nothing old fashioned about the spec, though, which is bang up to date netbook standard: 1.6GHz Intel Atom, 1GB of DDR 2 memory, 120GB hard drive, 802.11b/g Wi-Fi, 10/100Mb/s Ethernet, memory card slot and three USB ports. The memory's installed as a 1GB DIMM in the machine's single slot, accessed by unscrewing a panel on the base.
The screen is a SCC-standard 8.9in, 1024 x 600, but it's glossy, bright and crisp - one of the best netbook displays we've seen, in fact. The matte black bezel - complete with webcam - helps accentuate this.

Extended-run battery included
Toshiba's engineers was clearly more inspired by the 8.9in Eee PC than any other netbook, because the two machines are very similar. The size-defining component in a nine-inch netbook is the keyboard, and the one here is small like the Eee's rather than near full size, as you'd find on an Acer Aspire One or Sony Vaio P. It's got a solid underpinning, but on our review sample the left-hand lower corner was rather rattly - another Eee trait.
