This article is more than 1 year old
MSI mobo ditches Bios for EFI
Inside the future of PC set-up technology
The Game option is unusual as it allows you to play simple games in the UEFI that you load from CD in the limbo before the OS loads. This is similar to the Asus' Express Gate system, which allows you to use instant messengers and look at photos without booting your OS, so we asked Iain Bristow, who looks after the marketing of PC components at Asus UK, about the company's plans for UEFI

It even has... er... games
"We do plan on using it someday," he said, "but we’re not in a hurry. Currently, we aren’t seeing any huge improvements to end users [in implementing EFI].
"EFI’s major benefit is within its programming structure. It’s really good for the guys doing the designs, but to the end users everything that is available within EFI at this moment, we can do with Express Gate. We’ve been debating a GUI Bios for a long time, and we’ve done it before – currently it’s not that important to an end user, so we’ll focus on producing strong Bios."
Those are fair points, so we put a few questions to Richard Stewart, Marketing Manager at MSI UK. Yes, he admitted, at a simple level, EFI is just a 'pretty' Bios. "At this stage, the MSI Click Bios is just a tool to show what the future holds. As you click through it, you'll just notice all the 'legacy' menus and almost the same options but in a clickable format. You can, however, see new options such as language selection.
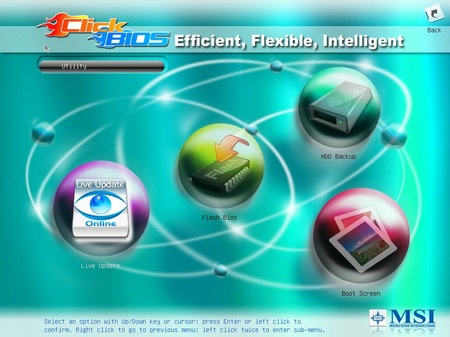
The Utilities section is more useful
"This is the next-generation Bios structure that moves away from the 25-year-old or more Assembly-based design into a new, very user friendly interface where you can even use a mouse. As development becomes more widespread we hope that within the UEFI framework we can activate the LAN (as an example), which would potentially mean the use of IM software, browsers, media players all available OS independent.
