This article is more than 1 year old
Doctor amputates boy's arm using SMS instructions
TXT 'ARM OP' to 80008
A British surgeon has performed an arm amputation on a 16 year-old boy, using instructions sent to him by text message.
Nott amputated the boy's arms using SMS instructions
David Nott, a volunteer for the French medical charity Medicin Sans Frontierescame across the boy in the Congo, Africa whose arm went gangrenous after it was bitten by a hippo, according to a report by CNN.
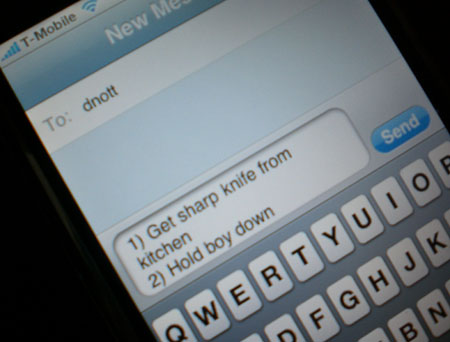
The operation was very complex and required the boy’s collarbone and shoulder blade to be removed. Nott needed guidance on how to perform the task and so sent an SMS to Meirion Thomas a London-based surgeon who the conducts most of the UK's forequarter amputations.
Thomas replied with a 10-step guide for the operation and signed off with “Easy! Good luck!”
“I just got on with it, and everything he told me, I just did,” said Nott.
The boy survived the operation and has since made a full recovery.
It’s unclear if Thomas’ 10-step guide to arm removal will be released as an SMS subscription. ®
