This article is more than 1 year old
How to customise the Acer Aspire One GUI
Get the look you want
Each entry points to a .desktop file which tells Linux what to do when the icon is clicked. It also tells Linux and the AA1 UI what icon image to display, but you can change that by adding an icon=filename.png into the <app...> tag. We downloaded series of 512 x 512 .png files from the net, used sudo cp... them into /usr/share/pixmaps/ then added them to the appropriate group-app.xml entries. Look for .png files that are at least 128 x 128.
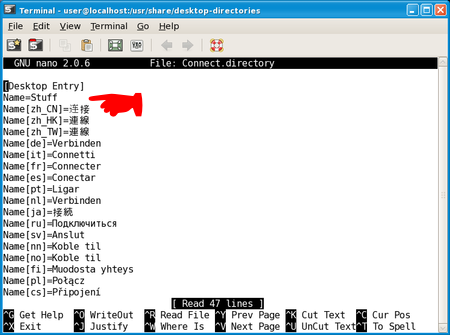
Change this line in Connect.directory to alter the Connect panel's name
How did we change the panel titles? By editing the relevant .desktop files in /usr/share/desktop-directories/ with sudo mousepad /usr/share/desktop-directories/Connect.desktop for instance. Inside the file, you'll see a Name= field - change this from Connect to, say, Internet. Save the file and restart the AA1 to see the change.
Editing the various .desktop files referenced in group-app.xml - always with sudo - will let you change how the icon is subtitled on the desktop (change the Name= entry) and the tooltip that appears when you hover the mouse pointer over the icon (change the Comment= entry).
The other fields govern how the app's loaded, so you should leave these alone.
At this point, you're possibly thinking you can replace the various panel and titlebar graphics with your own. Since they're .png files, why not replace them with fully transparent images and have your icons 'float' over the desktop?
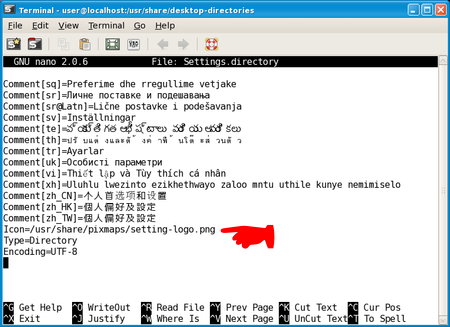
Change this line in Settings.directory to alter the Settings link's icon
We tried it, and the AA1 refused to play ball. Acer's code appears to expect the pre-loaded graphics to be used. If they're not, it defaults to single-colour panels. We made sure our images were the correct sizes, had the right permissions and used the RGB colour model as the pre-loaded ones do. Still no joy.
If anyone - Acer software engineers, in particular - has any insight into get past this apparent restriction, we'd love to hear from you and will update this piece accordingly.
The Netbook Newbie's Guide to Linux
Episode 1: We're the Fukarwi
Episode 2: One small step for Man...
Episode 3: The Big Easy
