This article is more than 1 year old
How to customise the Acer Aspire One GUI
Get the look you want
Now you've got your preferred background, you'll notice the AA1's search panel no longer looks correct. The easiest thing to do is remove it. Go back to the terminal window and type:
sudo mousepad /usr/share/search-bar/start-search_bar.sh
You'll get an 11-line bit of code that tells the AA1 where to place the search bar depending on the screen resolution. Just add a # to the start of every line, and when the script is activated at start-up, the bar won't be placed.
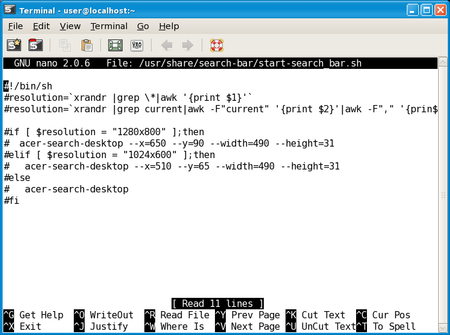
Editing start-search_bar.sh in nano
Alternatively, you may want to experiment with those --x= and --y= values after the acer-search-desktop command to put the search bar in a different part of the screen.
The files the AA1 desktop control app uses are hidden from the File Manager, so they have to be initially accessed through the terminal. In fact, since they need to be owned by the system's über-use, root, it's best to use terminal and its sudo command - which makes your commands appear is if they were entered by root - throughout.
The key configuration file is group-app.xml, and it's stored in the /home/user/.config/xfce4/desktop/ folder. So, in terminal, type:
cd /home/user/.config/xfce4/desktop/
then
sudo mousepad group-app.xml
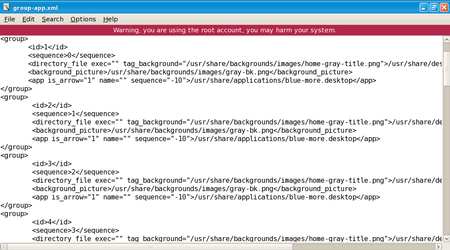
The main screen panel 'groups' in group-app.xml
Acer's programmers didn't leave group-app.xml as tidy as they might, so we recommend separating out the various sections with blank lines to make them easier to find and focus on in future.
The important bits are in the various <group>...</group> tags. The first four deal with the four panels you see on the main desktop. The next four list what icons each of these contain.
