This article is more than 1 year old
25 years of Macintosh - the Apple Computer report card
What Steve hath wrought (from A to F)
iTunes and the Halo Effect
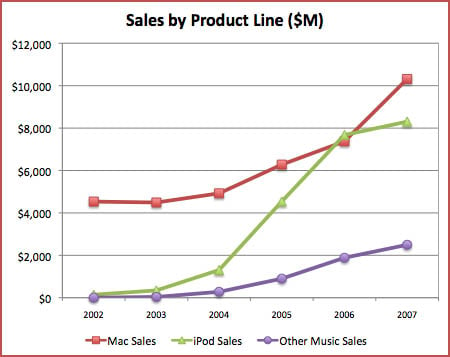
Here's our final excursion into Excel's charting capabilities. Up to this point we've ignored Apple's non-hardware sales. Now we take a look at what we call "Other Music Sales" and what Apple calls in its 10-K filings "Other music related products and services" and defines as "iTunes Store sales, iPod services, and Apple-branded and third-party iPod accessories."
Apple other
Although Apple's financial reports don't break this figure out in any more detail, we aver that the iTunes Store accounts for the overwhelming majority of these sales. After all, the iTunes Store sold its 5 billionth song on June 19th of this year - it wouldn't have required a lot of help from "Apple-branded and third-party iPod accessories" to reach $2.5 billion in "Other music related products and services" in 2007. (Break-out product-line figures for 2008 will not be released by Apple until it files its 2008 Form 10-K at the end of this year).
Notice also that in 2006 iPod net sales passed Mac net sales before beginning their inevitable market-saturation plateauification in 2007. Apple gambled that the iPod's much-vaunted "halo effect" would begin to drive Mac sales upward before the iPod climbed atop its sales-growth mesa. They won that gamble.
Jobsian Other Growth: A-
One final thought about these metrics: Although the world economy is swiftly flushing itself down the crapper, Apple's impressive $25bn in cash reserves will help it weather the reduced consumer and business spending during the expanding fiscal hideousness. When the current economic tsunami finally recedes, Apple should be in a far better position than many of its washed-out-to-sea competitors, especially in the music-download and smartphone spheres. ®
Rik Myslewski is the former editor in chief of MacAddict and former executive editor of MacUser. He joins The Reg full-time on December 1.
