This article is more than 1 year old
Still sending naked email? Get your protection here
Buckle your seatbelt, encrypt your bits
Get more from Enigmail
Enigmail can be used for several other purposes, including adding your contacts' public keys to the keyring. The plug-in should automatically detect emails that include a public key and invoke a pop-up prompting you to add the key. Contacts whose public keys have been added to your keyring are then able to sign messages that prove they were generated with the corresponding private key. Such messages look like this:
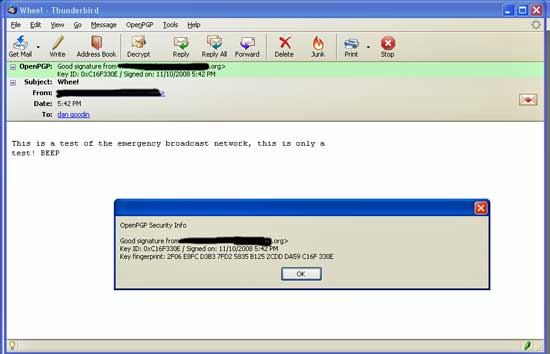
Emails signed with a sender's private key guarantee its origin
You can also digitally sign messages you send to others using the OpenPGP button that now appears on Thunderbird's composition window and, if you've got the public key of a recipient, you can also send that person an encrypted email.
