This article is more than 1 year old
Still sending naked email? Get your protection here
Buckle your seatbelt, encrypt your bits
Step 1: Installing Gpg4Win
Navigate to Gpg4Win's download page and download the latest full version of the program. At time of writing (and indeed since November 2007) that was gpg4win-1.1.3.exe.

Gpg4Win download page
Whenever you're installing a piece of software this sensitive, it's a good idea to verify that the program you've just downloaded is the real thing by checking its SHA1 or MD5 checksums. SlavaSoft's HashCalc is one reliable way to do this. Download and install it, and then compare the checksum it computes for gpg4win-1.1.3.exe against the checksums provided here.
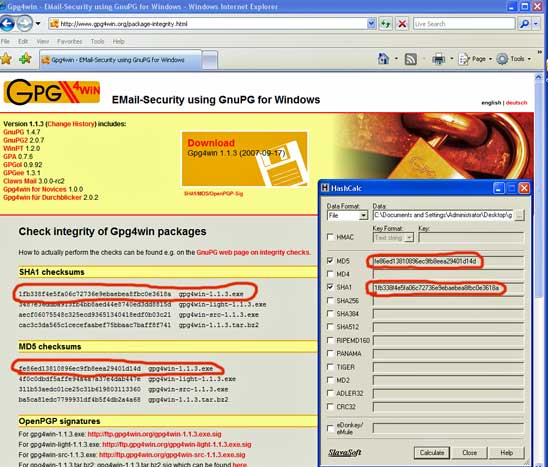
Verify the gpg4win executable is legit
Once you've verified the integrity of the exe, double click it to install. You will now be presented with a screen of components to install. They include:
- GnuPG: its key component, the encryption software
- GPA: GNU Privacy Assistant, a key manager
- WinPT: Key Manager, which also supports encryption via your Clipboard
- GPGol: a plug-in for Microsoft Outlook which integrates the operation of GnuPG
- GPGee: a plug-in for Windows Explorer which allows encryption of data by right-clicking on your mouse
- Claws Mail: a complete email program with integrated GnuPG operation
(I couldn't find GPGol in my setup, but I didn't care since it only works only with Outlook 2003).
