This article is more than 1 year old
HPC data center glory? It's in the game
Everything but the homicidal IT admin
Most people's visions of data center domination need to be put on hold in today's floundering economy, but at least now there's a video game to keep the dream alive.
To build excitement for its participation in this year's Supercomputer conference, Purdue University in Indiana has made an online game that finally offers a taste of stacking big silicon.
Rack-A-Node challenges players to build a cluster supercomputer using various computer types to process science experiments. If the jobs are successful, players receive additional funding to build an even bigger system.
"Like the game 'rock, paper, scissors,' certain tools perform better against certain challenges," said Kyle Bowen, infomatics manager for Information Technology at Purdue. "In Rack-A-Nodeƒr, the player has to optimize the supercomputer for the type of science being performed."
For example, chemistry jobs require more memory, whereas climate-modeling needs faster network communication. Other tasks dropped into the racks include the usual gang of HPC workloads like life sciences, pharmacy, physics, animation-rendering, and engineering.
The game was built to highlight team Purdue at the SC08 Cluster Challenge, where students compete in building effective HPC clusters on the exhibit floor.
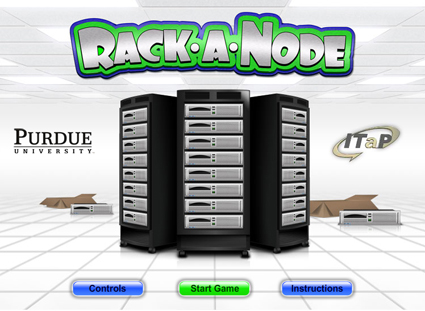
Image courtesy Purdue
Bowen told El Reg the Purdue group was inspired by playing various tower defense games and noticed a similarity between the genre and and the cluster challenge.
"We started developing the idea a week after last year's conference," he said.
A team of six at Purdue were recruited to build the game, lead by Jasen Fish (application programming), Michele Rund (user interface design), and Preston Smith, who heads the SC08 cluster team.
"What we looked to do with the game is capture the fundamental decisions that the cluster teams face during competition," Bowen said. "We looked at what made one cluster more or less competitive. Each type of job performs better or worse based on how the cluster was designed. We took these elements and built them into the game — allowing players to upgrade their processors, memory, networking, and compilers. Each choice has an impact on cost, power consumption and performance."
Test your mettle metal at virtual high performance computing right here. ®
