This article is more than 1 year old
Japan gets build-your-own-dog robot kit
The G-Dog
“A dog’s for life and not just for Christmas,” most animal lovers proclaim around this time of year. But how about one that you can take to bits and shove in a cupboard when you get bored with it?
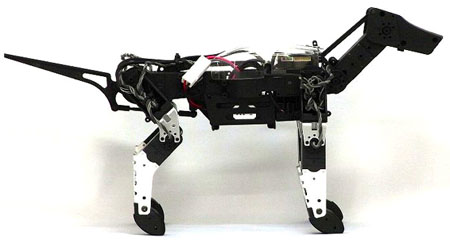
G-Dog is an animal/techno lover's delight
G-Robots’ G-Dog isn’t as cute as the Andrex puppy, but the mechanical pet can perform all sorts of clever tricks to keep you amused all the way through until Boxing Day. For example, it can push its hind legs up in the air and waggle them about, while balancing on its front... er... paws and face.
You can't blame farts on this pooch
We don’t think it’ll fetch the newspaper or bark at intruders. However, the puppy does sport 300° of movement and is controlled with a PS3-style remote.

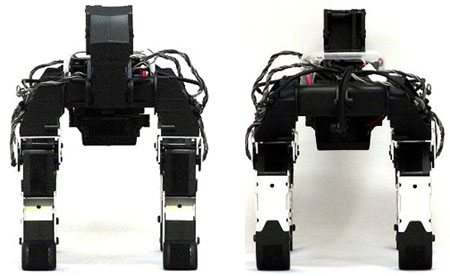
G-Dog comes flat packed
It’s worth noting that, from the looks of G-Robots’ sales website, this robotic pooch doesn’t come ready assembled. So you may find yourself spending most of Christmas screwing the parts together, which include aluminium brackets, a processing unit and nine “RS304MDs”.
G-Dog weighs in at 570g and measures 375 x 135 x 90mm. There’s no optional furry coat to make it more realistic, but at least you won’t have to feed and clean up after it.
Japanese techno pooch fans will can bag a G-Dog online for ¥70,000 ($705/£445/€545). A UK release date or price hasn’t been announced.
If you want to see G-Dog in action then click here for a video (WMV).
