This article is more than 1 year old
Asus N10 notebook-not-netbook
Best of both worlds - or the worst?
Review How do you approach the Asus N10? With its 1.6GHz Intel Atom N270 processor and 10.2in screen, it's a netbook. But it's not small, it's not cheap and it runs Windows Vista Business. So is it a notebook?
There's no question, however, that this notebook-not-netbook is a very sexy laptop that has 'premium product' stamped all over it, even though it's not priced like one
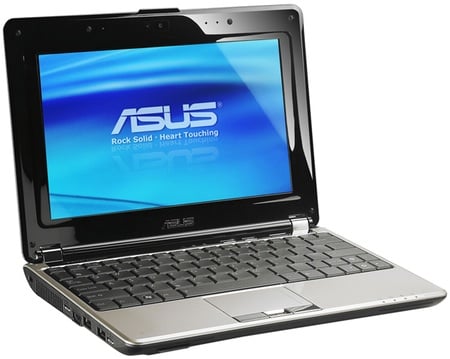
Asus' N10: notebook or netbook?
Fresh out of the box and unwrapped, the N10 immediately appeals with its glossy gunmetal-look lid, a covering that's used to deck out the wrist-rest area and keyboard surround too. Between this is the chrome hinge - the trackpad buttons and, between them, the fingerprint reader are chrome too. The sides and base of the machine are clad in matte black plastic, while the screen bezel is gloss black.
The N10's sides are home to the usual array of netbook ports: VGA, Ethernet, a USB 2.0 trio and 3.5mm audio sockets - one of which doubles up as an SPDIF port - but they're joined by an HDMI port and an ExpressCard 54 slot. The front of the laptop's base curves sharply away from the edge but is where you'll find the SDHC memory card bay and two slotlike speaker ports.
The curves at the front and back give the N10 a profile not unlike that of the MSI Wind, but this is a larger laptop than that one. It feels more like a 12.1in machine than one of the bigger netbooks, but while Asus has taken advantage of that to equip the N10 with a good-sized keyboard, it's a real shame it didn't do the same with the screen. You'll have to look to other machines in the N series for that.

Nice 'n' shiny
It's a 10.2in panel with the usual 1024 x 600 netbook resolution. But there's at least an inch of bezel all the way round it, room enough for a 12in, 1280 x 800 display. As it is, the screen looks a little lost among all the piano-black gloss, and the overall effect is to make the display seem smaller than it is. For those with weak eyes, the N10 has a key that pops up an on-screen magnifying glass that zooms to 2x with the first click, 3x with the second then magnifies the entire image with a third.
