This article is more than 1 year old
Nokia 7310 Supernova candybar phone
Swappable covers make a comeback
The controls around the phone's sides are limited to the volume rocker – there are no dedicated camera or music player keys. There is a earphone socket, usefully placed on the top of the phone next to the micro USB connector, but it’s a 2.5mm job, so to use your own headphones rather than the average in-box set, you’ll need to get an adaptor. This socket can also be used for a TV-out option – though there’s no cable supplied with the phone.
The phone’s menu and control arrays are classic Nokia Series 40. The home screen presents an Active Standby layout including a five-icon row of shortcuts on the top of the display, all of which can be changed.
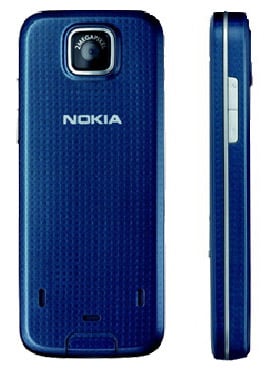
Photo quality is disappointing, even for this grade of phone
The two-megapixel camera isn’t a stunner. There’s no autofocus system or flash, and when shooting on the highest resolution setting, the camera can take around 15 seconds to finish processing images after you've pressed the capture key - not impressive.
Image quality is generally disappointing, even for this grade of phone. Shots are soft, with grain and noise evident. Colours are bright but can be oversaturated in strong light. Auto metering doesn’t seem to cope particularly responsively to changing lighting situations, and images can have colour tints or look washed out.
Nokia has included its usual array of settings to adjust, plus basic on-phone editing tools, but the results you can achieve with this camera are very limited. The 7310’s video capture abilities aren’t up to much either. Shooting in maximum 176 x 144 resolution, you get pretty low quality footage.
The music player is reasonable, though. The 32MB of on-board storage can be boosted with Micro SD cards of up to 4GB, though Nokia hasn’t included one in the standard package.
