This article is more than 1 year old
Dell Inspiron Mini 9 with Vodafone HSDPA
The best netbook with integrated 3G goodness
Review Dell may be late to the netbook party, but it's turned up with something very fashionable on its arm to make up: the Inspiron Mini 9, bulging in all the right places with HSDPA 3G mobile broadband goodness.
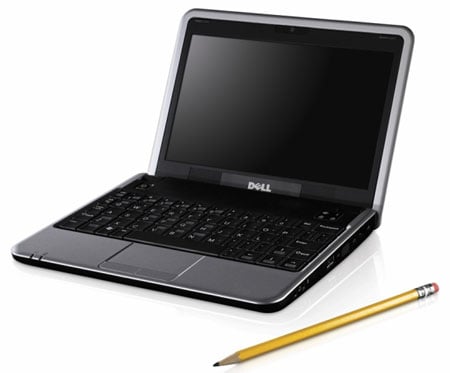
Dell's Inspiron Mini 9: now with HSDPA, courtesy of Vodafone
Unlike the Advent 4213 we reviewed recently, which also comes with HSDPA and into which you can slip any old 3G-enabled SIM card and surf away, the situation with the Mini 9 is a little more complicated. Although you can order one direct from Dell for £269 for the Linux version or £299 for the Windows XP flavour, neither comes equipped with 3G.
If mobile internet is what you're after, then your only option is to get one from Vodafone. On the plus side, the carrier will give you the Small, Cheap Computer for free. In exchange, however, you'll have to promised to cough up at least £25 a month for the next two years, which works out at £600 minimum for the 1GB-a-month deal. If you need to transfer 3GB a month then the £30-a-month commitment will cost you an additional £120 over the life of the contract.
While the price seems reasonable if you need a mobile broadband connection, the contract does seem a little on the lengthy side - two years is a long time in the life of a laptop.
Apart from baked in 3G, the Vodafone-branded Mini 9's spec isn't all that surprising. It's powered by a 1.6GHz Intel Atom N270 processor and 1GB of DDR 2 memory. The screen stretches to 8.9 inches and packs in a standard 1024 x 600 pixels. Dell has gone down the solid-state route when it comes to storage, opting for an 8GB SSD.
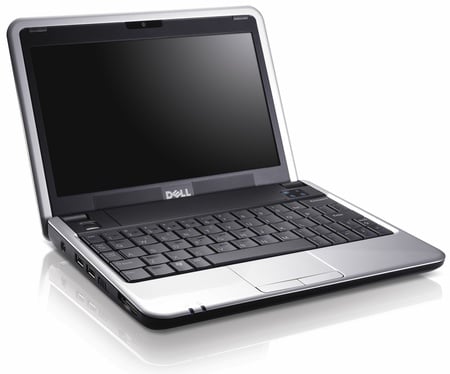
The best-looking SCC yet?
Completing the list on the wireless front, there's both Bluetooth and 802.11b/g Wi-Fi for your cableless communication needs. You'll find the usual three USB ports on offer - two on the left, one on the right - plus VGA, SD/Memory Stick slot, wired Ethernet plus 3.5mm headphone and microphone sockets.
