This article is more than 1 year old
Group Test: electronic book readers
Take your library with you when you travel
If you want any more info on the devices file support we'd suggest a shufti at the manufacturers' own websites as getting too deeply into this can seriously sap the will to live.
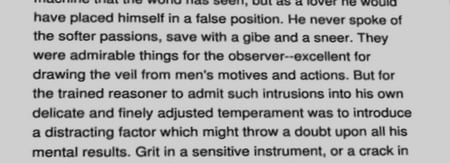
Text on the iLiad...
Once loaded with media, the Sony proves the most straightforward and intuitive to navigate around. Let's compare how you bookmark a page. With the Sony you press the bookmark button. Simple. With the CyBook and BeBook, you have to open menus and click about hither and thither. With the iLiad you don't do anything, because it doesn't support any type of bookmarking. Only the Sony lets you access all your bookmarks, no matter what book they are in, from a single, central menu.
The same is true of navigation to a specific page. On the Sony, you simply type the page number using the number keys – a feature we flat overlooked in our original review. Both the CyBook and BeBook require you again to open various menus, and while the touchscreen iLiad should make navigation easier you still have to pluck the stylus out of the back and remember which icon does what.
...the BeBook...
The iIiad's page-turn bar is an interesting bit of design, though: a long rocker strip that runs up the left side of the device that you nudge to the left and right. Its was set to turn pages forward with a right nudge and back with a left when we go it, which seemed a little counter-intuitive. But luckily, if you rummage about in the menus, you can swap the directions around.
The iLiad also has a “Wacom Penabled technology” touchscreen which only works with the supplied plastic stylus. Loose it and you can't access a fair chunk of the UI. A replacement will set you back £14!
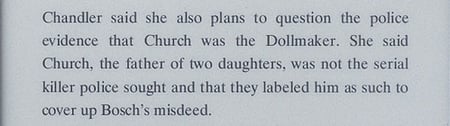
...and the PRS-505
Apart from having the most obvious navigation system, the Sony also has the fastest moving UI and menu system. While it certainly doesn't react as instantly as would the UI on an MP3 player, it does go about its business noticeably more briskly than the iLiad, CyBook or BeBook.
