This article is more than 1 year old
Intel Core i7 'Nehalem' processor and X58 chipset
We put the chip giant's new architecture to the test
If you overclock the base clock then all of the other clock speeds are affected but if you choose to work with the multipliers you can change the speed of one part of the processor without necessarily affecting another part.
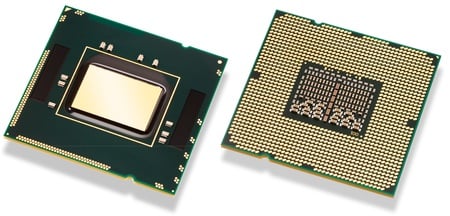
The Core i7 965: overclock block removed
The core of the CPU is the computational units, branch prediction, the cache, and other bits and pieces such as the registers. Everything outside the core is classed as the Uncore, but two big chunks of Uncore are the DDR 3 memory controller and the QPI link between the CPU and the system logic chipset's northbridge. That leaves some rather important odds and ends such as the L3 cache, power management and - potentially - integrated graphics.
Core i7 gives every indication that it's a modular design which can be developed in a number of different directions. So server chips might have even more L3 cache and QPI links, while a highly integrated desktop chipset could cut the amount of L3, slim down the memory controller and add a graphics core.
The area of the Core i7 die is a sizeable 263mm² which is larger than the 214mm² of the four-core Core 2 Extreme QX9650. Yet the Core i7 has few transistors than the Core 2 Extreme: 731m to 820m. No doubt the amount of cache in the two generations of processor is responsible for one of those changes, as the QX9650 has 12MB of L2, while Core i7 has 256KB of L2 cache per core and 8MB of shared L3 cache for a total of 9MB.
However, that doesn’t explain why the Core i7 die has such a large area so we’re going to take a guess that Intel has left space on the die to allow it to make changes to the feature set without a radical overhaul of the silicon.
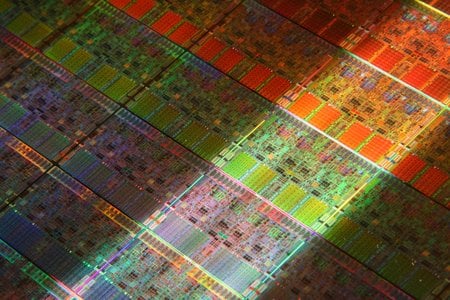
Die hard
An alternative explanation is that the apparent missing area is due to a change that Intel has made in the type of transistors that it uses in Core i7. The L1 and L2 caches contain eight transistors per memory cell which means the cache can use a lower power configuration. However, the larger L3 cache uses a traditional six-transistor-per-cell design.
