This article is more than 1 year old
The netbook newbie's guide to Linux
One small step for Man...
Episode Two This is a series about the Linux OS on netbooks, but we need to remind ourselves that these devices aren't personal computers. The personal computer is a machine you work on. Netbooks are essentially machines you work through, out into the Cloud.
It shouldn't matter what the operating system is. Or the hardware. Ideally, all your apps and your data are 'out there' in the Cloud, independent of any hardware or software you might use to access them. But design goals seldom accurately second guess the actual use to which things like these are put. We are treating these netbooks as low-cost PC - we are messing with the operating system and expecting to tailor them to our individual requirements. The legacy of the PC invites us to do so.
A corollary of this is that it would be idiotic to use these below-the-waterline adventures of ours either as evidence that netbooks are inadequate out of the box - or that Linux sucks.
Our first adventure took us down to the command line, where we explored a few of the available software tools. Linux is essentially layered like an onion: at the centre is the kernel, responsible for rudimentary connections to the hardware; wrapped round that are a set of Unix-like command-line software utilities; and on top of all this sits the GUI.
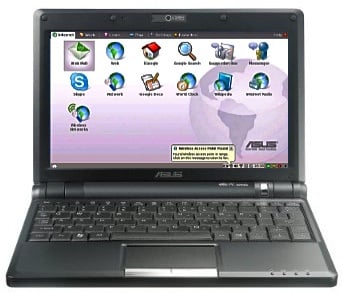
The three Small, Cheap Computers I'm juggling with at the moment: the Asus Eee PC 900, the MSI Wind and the Acer Aspire One (AA1). They all look as if they have completely different operating systems. Not so. The underlying kernels are virtually identical; the supplied software utilities are very similar but with some minor differences in their deployment.



Different GUI, same foundations: the Eee PC's Xandros (top), MSI Wind's SuSE (middle) and Acer Aspire One's Linpus
The main difference is the GUI, itself a layered system, with some very remarkable properties. Which is why it makes sense to focus initially on those command line utilities, if only because they provide common ground across all the Linux systems we are looking at.
|
Unix as Literature
Command line-averse users might do worse than read Thomas Scoville's article Unix as Literature here. It may not convert mouse-pushers, but it will at least give them some idea of where the key-tappers are coming from. |
