This article is more than 1 year old
Samsung Innov8 i8510 eight-megapixel cameraphone
Samsung's best smartphone yet
Although the 3.5mm socket allows you to add your own headphones, the supplied in-ear set are rather good, coming with a selection of swappable plastic tips to ensure a snug, comfortable fit. Our only niggle would be that we’d have preferred the 3.5mm socket on top rather than on the side of the phone.
Copying tracks over is fairly straightforward, either using the supplied Samsung PC Studio software, drag-and-dropping from a PC in mass-storage mode, or by slipping in a pre-loaded memory card. You can download tracks too, and the phone has a decent FM radio.
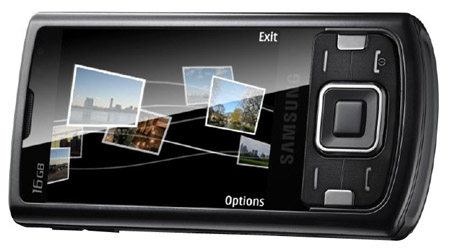
With nicely rounded edges, it slips into the pocket easily
A-GPS location finding is fast becoming a high-end mobile must-have, and it’s present on the i8510. You can 'geotag' your images with location data, so you can view on a map precisely where pics have been taken.
Google Maps enables you to pinpoint where you are, search for local amenities and places of interest, and plan routes, following them as you progress. It’s a very handy app to have on a phone, as we’ve mentioned before, but it isn’t a full satnav system.
On that score, Samsung's pre-loaded Route 66, though to use it you’ll first need to subscribe to Route 66's mapping, routing and voide guidance service.
We found the A-GPS gadgetry on the i8510 took slightly more time to get a full satellite fix in comparable locations than Nokia's N95 8GB and 6210 Navigator did. When it did lock on to our position, though, it held on well and was very responsive to our movement.
The i8510’s high-speed HSDPA and Wi-Fi connectivity ease the way for fast web browsing as well as swift downloading. The web browser provides a good web experience - you get page overviews and there’s Flash support. The i8510 can also handle RSS feeds.
