This article is more than 1 year old
Apple MacBook Pro 15in
A powerful, professional piece of kit
Like the standard MacBook, the MacBook Pro also includes a built-in webcam, along with two USB 2.0 ports, digital audio input and output, Gigabit Ethernet, 802.11n Wi-Fi and Bluetooth 2.1. It has the same large trackpad, made out of a small glass panel that acts like one big mouse button, along with the ability to use multi-finger gestures to control tasks such as right-clicking or quickly switching between applications. However, there are also a few other small differences that separate the MacBook Pro from the less expensive MacBook.
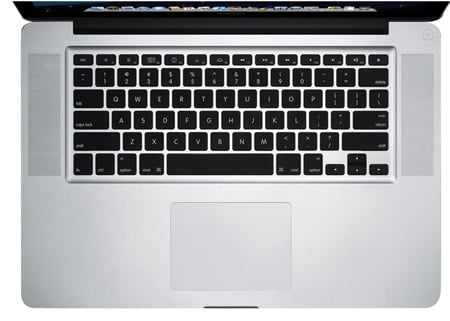
The large trackpad acts like one big mouse button
Long-time Mac users who noticed the lack of Firewire in the new MacBooks will be relieved to see that the MacBook Pro still has a Firewire 800 port. This provides almost twice the data transfer speed of an ordinary USB 2.0 port and there are lots of designers and video editors who use Firewire disks in their work, so this remains an important option for many Mac users. For these guys, that alone will justify the £250 price differential.
The MacBook Pro also has an ExpressCard 34 slot, which the standard MacBook lacks, for additional accessories and upgrades.
We were a little worried that the new MacBook Pro would have a built-in battery as the MacBook Air does. But we were relieved to see that the power pack is easily accessible through the base of the unit. In fact, a minor redesign here puts the hard disk, battery and memory slots all behind a single removable panel.

More ports than the standard MacBook
The battery indicator that used to be on the base of the unit is now on the left-hand edge, making it much easier to quickly check the battery level, while the DVD drive has been moved from the front to the right-hand side.
