This article is more than 1 year old
Google reports itself for aiding and abetting malware distribution
Search engine self-flagellation
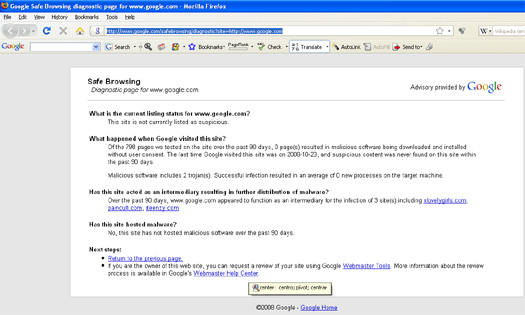
Google has castigated itself for being an intermediary for malware.
The search giant's Safe Browsing diagnostic tool reports that google.com avoids spreading malware directly itself but did act as an "intermediary for the infection of three site(s) including xlovelygirls.com, paincult.com, iteenzy.com" over the last 90 days.
Security experts we contacted about the rating were more puzzled that since Google indexes the whole web - and hackers are always trying to game its systems to increase the search engine rankings of sites harbouring malware - more brushes between Google and malware weren't listed. In fairness, Google has recognised and attempted to thwart this issue using tools such as its, err, Safe Browsing tool.
In other developments in this area, Google recently revamped its Webmaster Tools software so that it runs tests to determine if a site is hackable. This might arise, for example, if site admins are using a vulnerable version of WordPress as a blogging tool. Google's Webmaster Tools offer a service designed to help webmasters to see their site from the Google's perspective, facilitating the easier diagnosis of potential problems. ®
