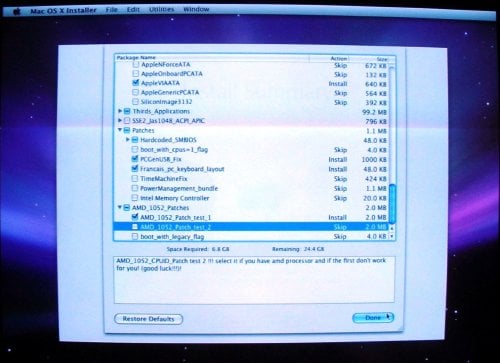
More detail from the Configuration screen.
If your computer has an AMD CPU, pick one of patches listed under "AMD_1052_Patches". If the OS install bombs, try again with the other one. When finished, click Done.
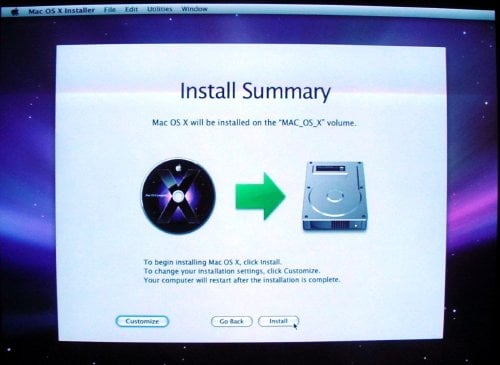
Back at the Install Summary screen, click Install
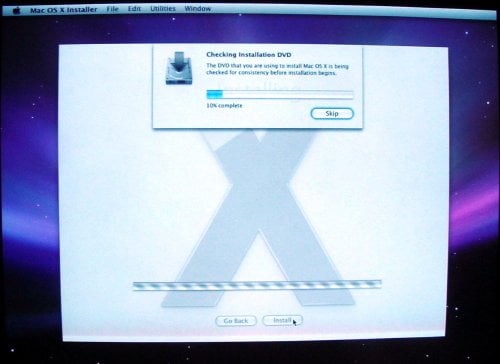
Checking the DVD is optional, and can be skipped
The installer spends a few minutes checking the DVD. This can be skipped, but let it verify the media the first time it's used. There are enough variables in installing OS X as it is. Bad media shouldn't be one of them.
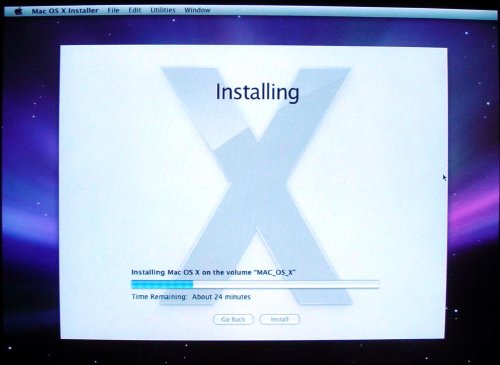
Like every OS installation progress bar ever made, this one lies. The actual install took 20 minutes.
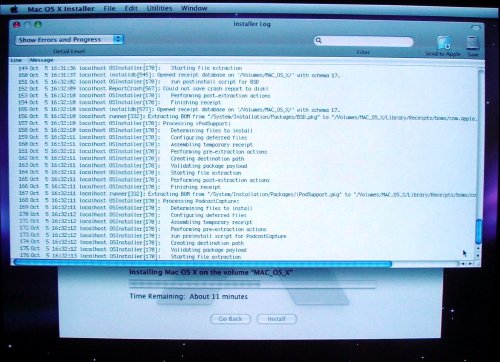
If you're not feeling geeky enough watching the graphical progress bar, click Installer Log under Window and get a more detailed view of the installation process.
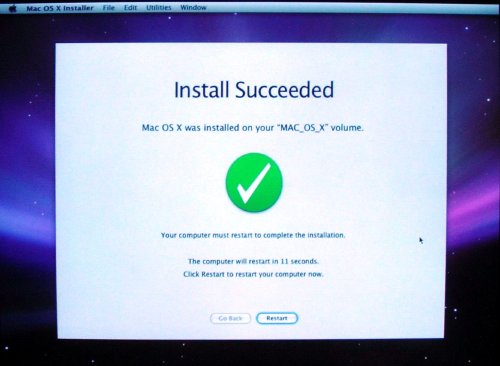
You've made it! Maybe. Click Restart to find out if the installation was a success
