This article is more than 1 year old
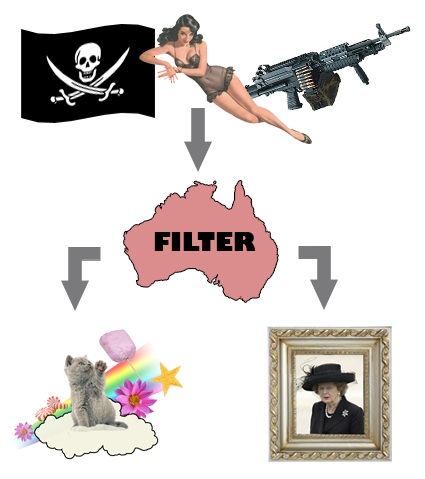
Oz watchdogs howl over 'Cyber-Safety' net filter
Can you opt-out?
Aussie civil liberties watchdogs are warning the country's "Cyber-Safety" internet filter plan won't actually let adults choose to opt-out from web censorship.
The Australian Labor party's $125.8m proposal is being pitched as a means to prevent children from accessing online pornography. The scheme includes a choice to opt-out, but many are now claiming the option won't in fact prevent internet censorship altogether.
Electronic Frontiers Australia (EFA) said even those who don't want their internet filtered will still be put on a second, secret blacklist designed to block "illegal" content.
"The news for Australian Internet users just keeps getting worse," said EFA spokesperson Colin Jacobs. "We have legitimate concerns with the creeping scope of this unprecedented interference in our communications infrastructure. It's starting to look like nothing less than a comprehensive program of real-time Internet censorship."
The concern appears to have its origins from a forum post by Mark Newton, a network administrator for the ISP Internode.
"The Government's plan is for there to be two blacklists, one for 'unsuitable for children,' and another one for 'unsuitable for adults,'" he wrote.
"The much-touted 'opt-out' would merely involve switching from blacklist number 1 to blacklist number 2."
"Under the proposal, there's no scope at all to switch to no blacklist at all. Regardless of your personal preference, your traffic will pass through the censorship box."
Reports of a secret secondary blacklist remain unconfirmed, due to the government's mixed messages on proposed opt-out provisions.
But the threat of such a system is enough to make pundits rather uneasy. Not only because the filter may incorrectly block websites or even controversial opinions, but because it may have an effect on Australia's internet speed and availability. ®
