This article is more than 1 year old
AMD Fusion for Gaming
Fusion debuts... as a software system speed booster
You need to have Overdrive installed on your PC, which in turn means that you need an AMD CPU, chipset and graphics card, and goes hand-in-hand with AMD's Catalyst drivers. There's no obvious reason why AMD Boost should require a specific make of CPU as it works with the OS, but AMD has clearly decided that its software will only work with its chips. Ironically, we found that Fusion worked correctly with the Phenom X4 9850 but refused to start when we installed an Athlon X2 4850e.
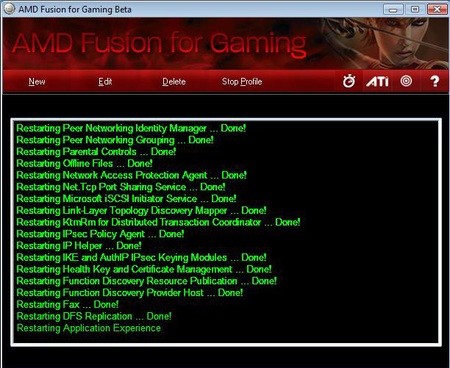
Finished gaming, your apps restart
The Expert profile not only shuts down superfluous software but also overclocks the CPU, chipset, graphics and speeds hard drive access but the difference that we saw in performance was absolutely negligible.
As the process is dynamic, we can’t be sure what FFG is doing to the clock speeds but we achieved far greater results by raising the CPU speed in OverDrive and then cranking up the graphics core and memory in Catalyst. In other words, the manual approach worked like a dream but it took a certain amount of work.
The big problem is that many of the apps FFG shuts down make such a small impact on your system - they pop up, grab a couple of CPU cycles of the 2,500,000 available each second, then go back to sleep - that they simply don't impede performance.
No doubt there is scope for Fusion to change before it comes out of Beta to work on the overclocking side of things, but for now this so-called utility appears entirely useless. We hope it's not a sign of what we can expect from the real Fusion.
Verdict
We like the idea of a one-click application that gets your PC ready for gaming but as things stand there’s room for improvement. Lots of room...

