This article is more than 1 year old
Dell Latitude E6400 14in business laptop
Dredd-ful new design?
That said, performance isn't really what the Centrino 2 upgrade's all about - it's more concerned with delivering a small performance boost while extending the battery life. But alas there's nothing special to report on that point. We ran out customary test - keep PCMark05 on the go until the battery is drained - got just over two-and-a-half hours out of it. That's equivalent, in our experience, to over five hours' real-world usage. Not bad, but not exactly amazing, either.
Tough enough?
Still, it's a solid base on which to build, and reducing the backlight level or using the ambient light sensor, and turning off one or both of the wireless radios, will push the effective run time well beyond that level.
Re-running test with the wireless disabled and a much lower screen brightness yielded three hours and 50 minutes using PCMark05, which is just shy of eight hours in real-world usage, maybe longer depending on your own usage pattern. Dell's claim that you can get ten hours out of looks possible.

DisplayPort for digital monitor connections
Speaking of power, mention should be made of the E6400's 15mm-thick power slab. It's not particularly small, but being a lot flatter than most AC adaptors is at least easier to pack away. The ends are concave to make wrapping the output cable around it easier.
Verdict
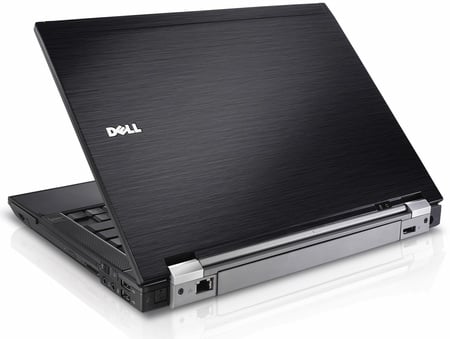
With its angular black mittel-Europa executive styling - BMW rather than Lexus - the Latitude E6400 certainly looks the part of a serious business machine. It provides all the connectivity - network and peripheral - you could wish for and decent performance, all at a surprisingly middle-management price. An excellent machine - as long as you're not intimidated by the styling. It is the law.

