This article is more than 1 year old
Messenger closes on Mercury for second fly-by
Cameras at the ready...
NASA's Messenger spacecraft is closing on Mercury for a second fly-by, during which it will snap 1,200 images of the planet's remaining unseen surface.
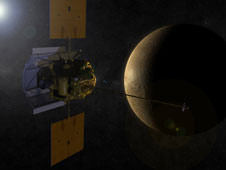 Back in January, Messenger's initial visit returned some nice photos of roughly 20 per cent of Mercury's hitherto hidden hemisphere. It approached to within around 125 miles (200km) of the surface, and will repeat this low-altitude sweep for its 6 October rendezvous.
Back in January, Messenger's initial visit returned some nice photos of roughly 20 per cent of Mercury's hitherto hidden hemisphere. It approached to within around 125 miles (200km) of the surface, and will repeat this low-altitude sweep for its 6 October rendezvous.
Louise M Prockter, instrument scientist for the spacecraft's Mercury Dual Imaging System, said: "This second fly-by will show us a completely new area of Mercury's surface, opposite from the side of the planet we saw during the first."
Among the treats in prospect are insights into the "unique physical processes governing Mercury's atmosphere, as well as additional information about the charged particles located in and around Mercury's dynamic magnetic field".*
Messenger's altimeter is poised to measure the planet's topography - "allowing scientists correlate high-resolution topography measurements with high-resolution images" - while scientists hope the fly-by will provide insights into Mercury's composition.
Ralph McNutt, Messenger project scientist at Johns Hopkins University Applied Physics Laboratory, explained: "We will be able to do the first test of differences in the chemical compositions between the two hemispheres viewed in the two flybys. Instruments also will provide information about portions of Mercury's surface in unprecedented detail."
Messenger has now covered more than half of the 4.9bn miles which will eventually end in orbital insertion around Mercury in March 2011. Before that, it's scheduled to make a third pass of the planet in September 2009. ®
Bootnote
*NASA notes that Mercury's magnetic field "appears to be actively generated in a molten iron core".
