Exclusive Baidu is renowned as China’s glittering internet success story, and as the start-up that gave Google a bloody nose. It dominates the web in the world’s second biggest economy with 70 per cent market share, and on Wall Street carries a market cap of almost $12bn.
But Baidu’s success comes at a price, for the legitimate music business, for the development of China and of its intellectual property (IP) law, and for any internet company wishing to do business in China.
Baidu owes its success to its MP3 Search service, which takes surfers directly to music. It’s known as “deep linking”, and early this year, sound recording owners represented by IFPI filed a copyright infringement case against Baidu, claiming damages worth $9m.
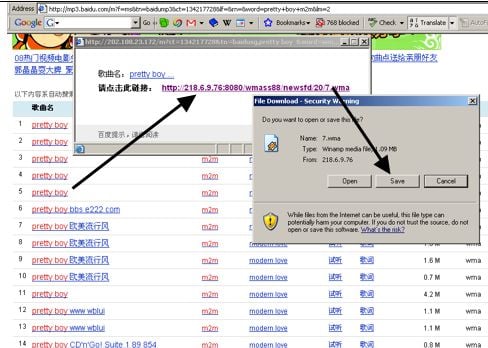
Baidu’s MP3 Search means downloads too
Yet the scale of Baidu’s operation, uncovered by a forensic six-month investigation conducted in China for The Register, has surprised the music business.
“Although we already had some doubts about Baidu mp3 search, when we saw the investigation results presented, it was really a shock," Susanna Ng, EMI Music Publishing Managing Director, Asia Pacific told China’s Fortune Times.
Music searches using Baidu return results that are heavily skewed in favour of unlicensed music, while they rarely return search results for licensed music sites. Meanwhile, the unlicensed MP3s appear to systematically move around a complex network of domains in response to infringement notices.
Chinese web surfers may be forgiven for missing the news. Baidu fails to link to news stories critical of the company, including some of the findings below; these have been covered only by a handful of publications within China. It’s a chilling reminder of the ability of a web search engine to control and shape public discourse.
We’ll explain what Baidu does, and why it’s in trouble. And the grim prospects for anyone hoping to build an internet business in China — with an unstoppable Baidu.
