15
This article is more than 1 year old
Intel X-25M solid-state drive
Stunningly Special SSD?
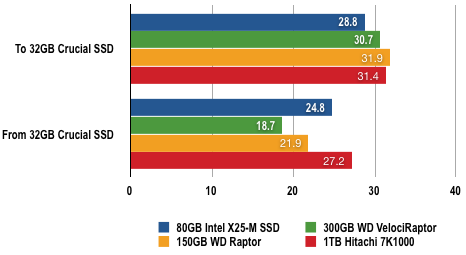
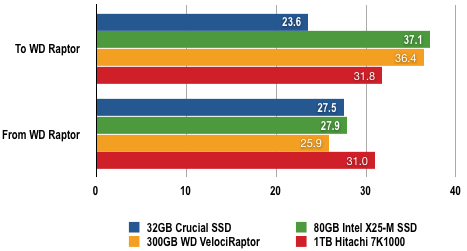
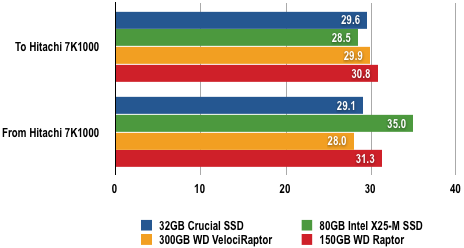
File-transfer speeds were generally very fast although there was a notable glitch reading files from the Crucial SSD as the Intel X25-M was slower than both the Raptor and VelociRaptor - although it was faster than the Hitachi 7K1000. It was apparent that the bottleneck in performance was the other drive, so the X25-M was able to stretch its legs with the WD Raptor. We have no doubt that it would have been truly stunning with the VelociRaptor.
Duplicate 2GB of Files on the Drive
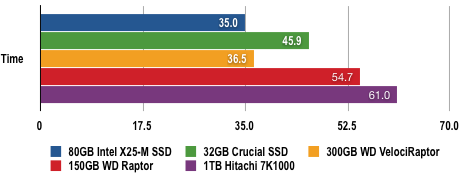
Shorter bars are better
File Transfer Results
Times in seconds
Shorter bars are better
