This article is more than 1 year old
Ten tweaks for a new Acer Aspire One
Take charge of Linpus
3. Enable the Advanced Menu
Acer's AA1 desktop doesn't display all the apps and options available to you. To get them all, you need the machine's so-called Advanced Menu.
Press Alt-F2 on the keyboard. This pops up a dialogue like Windows' Run... panel. Type xterm and hit the Run... button. A Linux command line will appear in a window - type in xfce-setting-show and hit Enter.
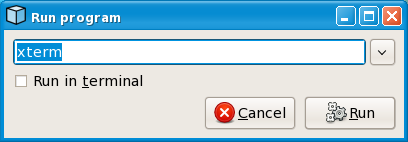
Linpus Run... window: activated with Alt-F2
XFCE is Linpus' GUI controller, and its Settings Manager will now be displayed. Click on the Desktop icon then select the Behaviour tab. Check the 'Show Desktop on Right Click' option then close each window.
Now when you're looking at the Acer desktop, clicking the right mouse- or touchpad-button brings up a menu listing all the apps and utilities you can use. Newly installed apps will also appear here.
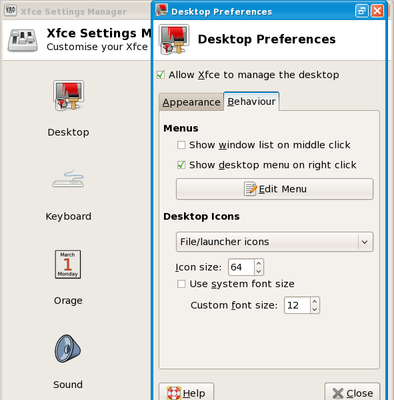
XFCE's settings window
4. Install The Gimp
The Advanced Menu contains a handy entry in the System sub-menu: Add/Remove Software. Select it then, when asked, enter the password you chose when you first started the AA1. After a moment, you'll be able to browse and search a list of programs you can download and install.
Here's a handy one: the GNU Image Manipulation Program, aka The Gimp. In the Package Manager's Search tab, type in gimp then scroll down to The Gimp's entry in the list that's displayed. Click on the check box next to it then on the Apply button.
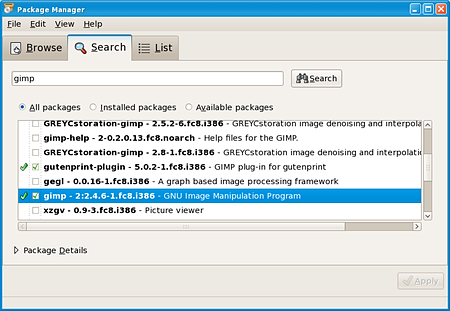
Linpus' Package Manager - aka 'pirut'
Package Manager will seek out other files that Gimp needs in order to run - tell it when asked to install these too. When everything's downloaded and installed, quit Package Manager. You'll find Gimp in the Advanced Menu's Graphics sub-menu, ready for editing photos or any other images.
