This article is more than 1 year old
Scotland's oldest newspaper exposes readers' smalls in public
URL manipulation snafu gives access to other users
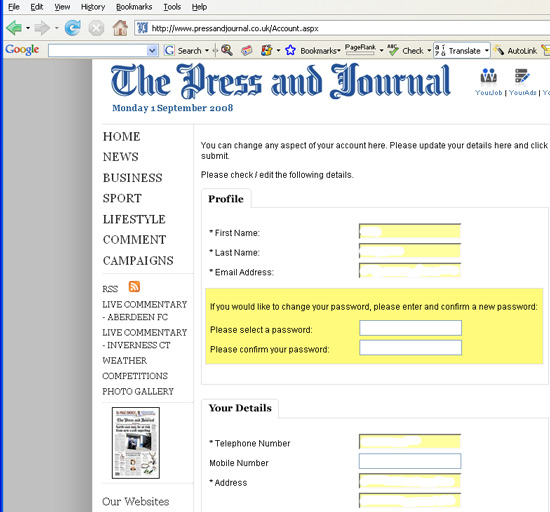
Updated Scottish newspaper The Aberdeen Press and Journal inadvertently made it easy to harvest sensitive information about registered users from its site as a result of a basic information security mistake.
Registered users are presented with stories an a URL along the lines of
http://www.pressandjournal.co.uk/Article.aspx/815191?UserKey=xxxx
By altering the UserKey number it was possible with only one further click of a mouse button to see the name, home address, email address and telephone number of registered users.
Granite City reader details exposed
Only registered users can make comments on stories or enter competitions. Registration also gives readers the ability to search through job and car adverts on affiliated sites, or to track online responses to ads.
The Aberdeen Press and Journal is the main local paper for Scotland's third city, and was first published in January 1748. Judging by the UserKey numbers its site has more than 80,000 registered users.
Parent firm Aberdeen Journals Limited maintains a privacy policy that states that "protecting the privacy and personal data of individuals is an important aspect" of how the firm is run. By allowing access to sensitive details via simple URL manipulation the paper has clearly fallen short of this policy.
The paper got its developers to fix the problem promptly, only hours after we relayed the concerns of Reg readers on Monday. "Apparently, the bug was introduced two or three weeks ago during an upgrade to part of the site," a representative of Aberdeen Journals explained.
Aberdeen Journals is far from alone in making a security slip-up that created a URL manipulation risk. Coding errors in O2's Bluebook application, discovered and repaired in February 2008, made it briefly possible to see SMS messages sent through the service by other registered users simply by changing the message ID number. Customers' call records of 02's business customers were left open by the same type of coding snafu in August 2006.
URL manipulation also cleared the way to viewing application forms submitted to oil giant Shell in 2003. More seriously still, Powergen fell foul of basic URL manipulation in July 2000, with the result that credit card payment details were exposed.
In reporting on previous instances of URL mainipulation we've been told that using the HTTP Post method of encoding a database query would mean that a requested page comes with a URL that looks like gibberish, reducing the problem of URL manipulation. Judging from your feedback, this is no longer best practice, if it ever was. ®
Bootnote
Thanks to Reg reader Frazer for first alerting us about the problem with the Aberdeen Journals site.
