This article is more than 1 year old
VPN security - if you want it, come and get it
Attention WiFi hotspotters: You want it
Configuring OpenVPN
Now it's time to add the configuration files to the server and client machines and modify them as needed.
Download a file called server.ovpn here and client.ovpn here. You'll need to rename the files server.ovpn and client.ovpn and copy them into the C:\Program Files\openvpn\config folders of your server and client respectively.
If you've followed our directions exactly, these files have most of the settings you'll need, but you'll have to add several of them yourself. To do that, start with the server, navigate to C:\Program Files\openvpn\config, and open server.ovpn in any text editor (for example, by right clicking on server.ovpn, and choosing Open with > notepad). Search for the text string "server-bridge". Immediately to the right, you'll find several strings that will have to be replaced with settings that are unique to your LAN:
Replace DEFAULT.GATEWAY with the IP number of the default gateway for your LAN. In our case, this number was 192.168.199.1. Replace SUBNET.MASK with the subnet mask of your LAN. In our case, the number was 255.255.255.0.
In the housekeeping section, we instructed you to find a chuck of IP space in your LAN's subnet that isn't being used by any other machines on your network. You'll need one for each client that connects. Replace BEGINNING.DHCP.RANGE with the first reserved IP address, and END.DHCP.RANGE with the last. When you're done, the line should read:
server-bridge 192.168.199.1 255.255.255.0 192.168.199.151 192.168.199.161
Be sure to save the file.
Now it's time to customize the configuration file for your client. Search for the text string "PLACE.IP.NUMBER.OR.DOMAIN.NAME.HERE". If you created a domain name using DynDNS, this is where it goes. Or, if the server has a static IP address, type it here. Be sure to leave a space between the domain name or IP address and the 443.
In our example, this section of the client.ovpn file will read:
remote openvpndemo.dyndns.org
Again, be sure to save the file.
If you've completed all the steps correctly, the C:\Program Files\OpenVPN\config folder on your server should look like this:
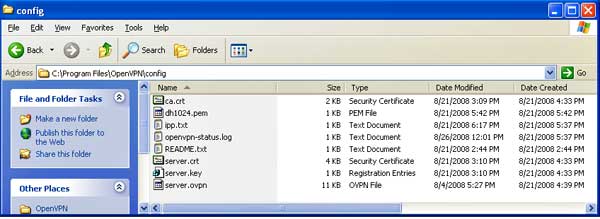
Server config folder after generating keys and adding config file
And the C:\Program Files\OpenVPN\config folder of your client will look like this:
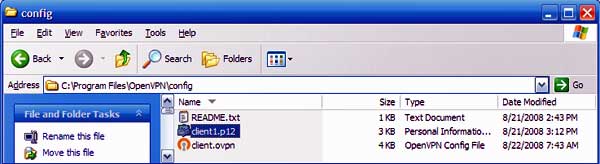
Client config folder after generating keys and adding config file
