This article is more than 1 year old
VPN security - if you want it, come and get it
Attention WiFi hotspotters: You want it
Your wish is your command window
Here's what your command window should look like once you've gotten this far:
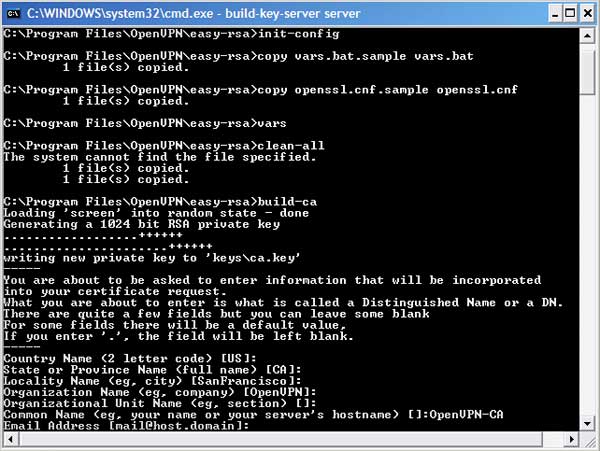
Command Window after generating certificate authority key
Now it's time to create the key for the server. To do that, keep the command window open and type:
build-key-server server
Like the last command, you'll be prompted for information. You can leave all fields, including the one asking for a challenge password, blank. The sole exception is the Common Name field. When queried for Common Name, enter "server". When asked to sign the certificate, enter y for yes. When asked to commit, enter y again. You have just created the key pair that will be used by your server.
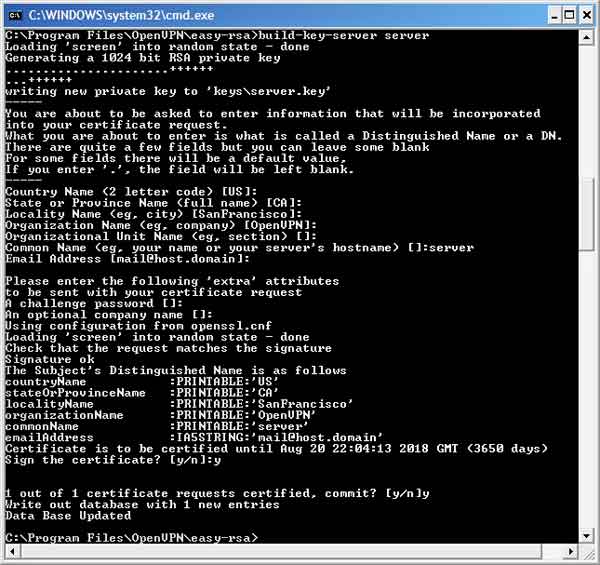
Command window after generating server key pair
Now it's time to create the key pair to be used by your client machine. To do so, keep the command window on your server machine open and type:
build-key-pkcs12 client1
This command will generate a key pair that can only be accessed by typing in a passphrase of your choice. As in previous cases, you can leave most entries blank, with the exception of Common Name. For that field, enter "client1". When asked to enter a challenge password, leave the field blank. When asked to sign the certificate, enter y for yes. When asked to commit, enter y again. Next, you'll be asked to enter and re-enter an export password. This step is important, because it will prevent a thief from accessing the VPN in the event the client computer is stolen. Choose something good, and be sure to remember what it is.
You have just created the key pair that will be used by your client.
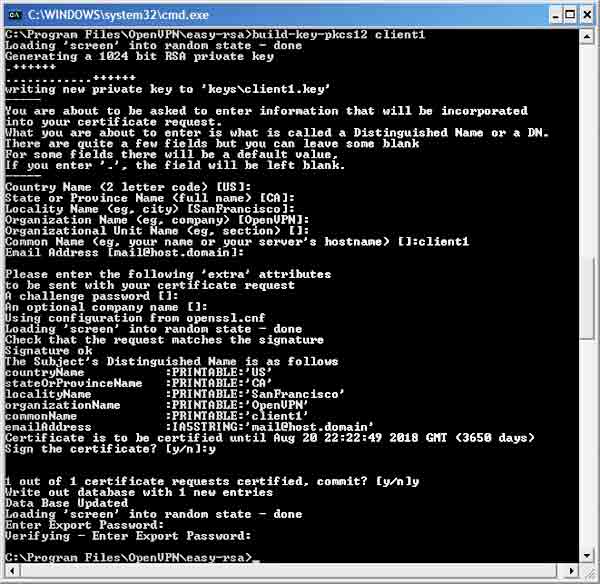
Command window after generating client key pair
If you've gotten this far, you've successfully generated all the keys needed to connect a client to a VPN server. Double click on the folder located at C:\Program Files\OpenVPN\easy-rsa\keys and you'll find the keys.
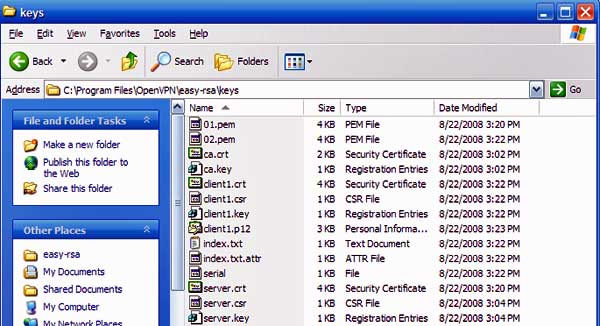
Keys folder after keys have been generated
Now, it's time to put the keys in the proper locations. The most important file in the entire bunch is the one titled ca.key. This is the certificate authority that is used to generate new keys for clients that connect to the server. If it's lost, it will be impossible for additional clients to connect to the VPN server. Even worse, if it's stolen, it will be possible for the thief to connect to the server. Keep the ca.key file in a highly secure location, i.e., one not connected to the internet.
The next three files to pay attention to are ca.crt, server.crt and server.key. Copy all three to the folder on the server machine located at C:\Program Files\OpenVPN\config. Finally, going back to the C:\Program Files\OpenVPN\easy-rsa\keys, locate the file called client1.p12. This file needs to be copied to the client machine, specifically to the folder located at C:\Program Files\OpenVPN\config.
You have now completed the key management part of setting up OpenVPN.
