This article is more than 1 year old
Breakup with Sadville lion ends in kidnap plot, duct-taped dog
Happiness is a warm laser sighted taser
In Sadville, they were close. But in our world, the relationship quickly took a turn for the worse. He dumped her. She walked into his office with a gun and tried to kidnap him. And when that failed, she broke into his apartment with handcuffs, some duct tape, a taser, a BB gun, and a dog named Gogi, shining some sort of "laser beam" onto his chest before he fled the scene and called the cops.
According to a Philadelphia-area TV station, local police in nearby Delaware have apprehended 33-year-old North Carolinian Kimberly Jernigan after she turned on her ex-virtual lover, a 52-year-old man who masqueraded as a lion while dodging flying penises inside Sadville.
They met on Sadville's virtual streets, but after the pair laid eyes on each other in our world, the virtual lion/52-year-old man ended the relationship, "sending Jernigan into a downward spiral."
Earlier this month, the North Carolinian allegedly drove to her ex-virtual lover's Pennsylvania workplace and attempted to kidnap him at gunpoint. But he got away. Then, two weeks later, she returned to Pennsylvania, posing as a postal worker in an effort to uncover the manimal's home address.
Four days later, investigators say, she found his apartment and broke in - alongside her dog. When her ex-virtual lover got home last Thursday, he "saw someone pointing an object at his chest that was projecting a laser beam."
We're guessing Jernigan sprung for something along the lines of the Air TASER® Weapon Laser Sight Weapon System:
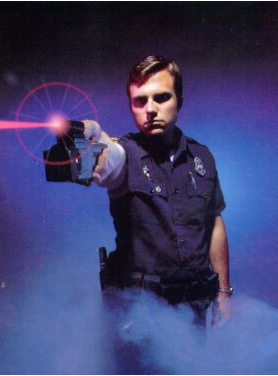
Air TASER® Weapon Laser Sight Weapon System (with some smoke and a faux cop)
When the police arrived, they found not only a taser, but a pair of handcuffs, a roll of duct tape, and a BB gun. And her dog was in the bathroom, duct tape around his jaw. Apparently, Gogi made a bit too much noise during the break-in.
About an hour later, Jernigan's vehicle was spotted at a highway rest stop, and she was taken into custody after a brief struggle. In our world, she faces charges of attempted kidnapping, burglary and aggravated menacing. In Sadville, she doesn't. ®
