This article is more than 1 year old
Alienware Area-51 m15x gaming laptop
Out of this world - or the laptop that fell to Earth
The four buttons are touch controls for Bluetooth, Wi-Fi, Stealth and Binary GFX. The first two are self-explanatory and the idea is that you rest your finger on the symbol for a second and the control toggles on or off as appropriate.
In practice, the touch control is a bit hit-or-miss and you’re likely to end up pressing it unnecessarily hard for what feels like an age. The problem is that touch controls look great but they’re far less practical than simple flick switches that you can eyeball to confirm whether they are on or off.
Stealth mode had us baffled at first as the m15x was delivered with it enabled so the CPU, memory and graphics performance were throttled to save battery life. With Stealth off – would this be Blatant mode? – the performance leapt up to the level that we expected, but the difference in battery life wasn’t as significant as we would have expected.
Battery Life Results
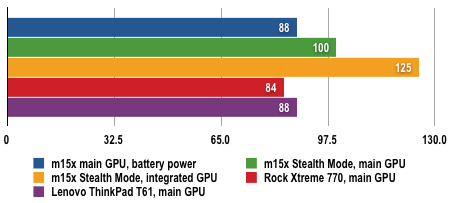
Battery life in minutes
Longer bars are better
The tests also show you really do need to ensure your m15x is plugged into the mains to get the best out of it.
3DMark06 Results
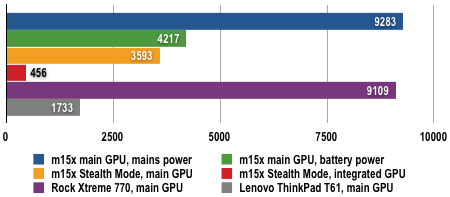
Longer bars are better
