This article is more than 1 year old
GTA: Chinatown Wars' features leaked online
Rockstar survey hints at DS game contents
Rockstar has been somewhat cagey about the features of its upcoming Grand Theft Auto videogame for the Nintendo DS. But some of the title’s qualities have since been leaked online.
Does this survey hint at the game's features?
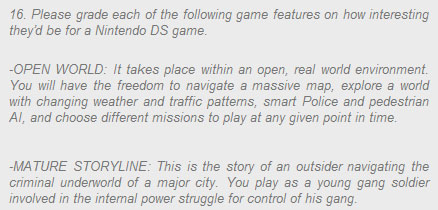
That’s if you believe a somewhat sketchy transcription of a customer survey, supposedly put out by developer Rockstar to discover what features players would like to see in Grand Theft Auto: Chinatown Wars.
Question 16 of the survey is all that’s been seen, but it asks gamers to individually grade the appeal of several different potential features. For example, the document makes reference to “an open, real world environment” where gamers have the freedom to navigate a “massive map” with changing weather and traffic patterns, police and pedestrians.
There’s also talk of players taking on the role of “a young gang solider involved in the internal power struggle for control of his gang”. Stylus based mini-games, such as one to assemble a sniper rifle, could also feature.
The survey extract first appeared on videogame blog UGO, but has since mysteriously disappeared. It may provide some valuable insight into the game’s potential features, but it’s also worth taking with a pinch of salt.
