This article is more than 1 year old
Tag Heuer teases with more Meridiist phone-cum-watch features
A clock that can make and take calls
Details about Tag Heuer’s first foray into the mobile phone arena have been sketchy, but they’re slightly clearer now as the watchmaker’s revealed more details about the upcoming phone-cum-watch.
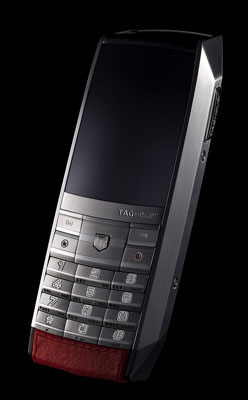
Tag Heuer's Meridiist: So many clock modes
Now we know what you’re thinking. “My phone already has a clock, why would I want to pay thousands for another one?” Well, does your phone’s clock boast a “bi-directionnal hour display dedicated to time” and a “chronograph measuring the 1/100th of a second, with a laptimer function”? Well, Tag’s Meridiist phone does.
The phone also features a perpetual calendar, which should be handy if you plan on living forever. Like no other phone on Earth, the Meridiist also has a world clock and, yes, an alarm function.

Did we mention it has a clock?
Yes, we know it all sounds pretty poncy. But the phone is quite stylish, according to the official pictures. For example, a secondary screen runs across the top of the handset and to display the date, time and incoming call details. The talker’s backing cover options include black rubber, red leather and crocodile skin.

Spot the subliminal messaging?
Tag hasn’t confirmed much about the phone’s technical capabilities yet, but it’s already been rumoured that the Meridiist will have a 1.9in main screen to display pictures snapped on its two-megapixel camera, which is protected by a sliding mechanical shutter.
If all that sounds a bit complicated though, don’t worry. Tag Heuer states that the phone’s start-up menu has been reduced to five entries – presumably so users don’t get stuck within sub-menu folders when all they wanted to know was the time.
An official price or release date still hasn’t been stated, but given that Tag’s confirmed that the Meridiist features 60.5 carats of Sapphire crystal glass, the previously rumoured €3900 (£3099/$6132) price-tag probably isn’t unrealistic.
