This article is more than 1 year old
Scareware package greets marks by name
Fakeale redux
Malware authors have created a strain of scareware packages that lifts the name of an infected user from the registry of an infected PC in order to create more convincing scams.
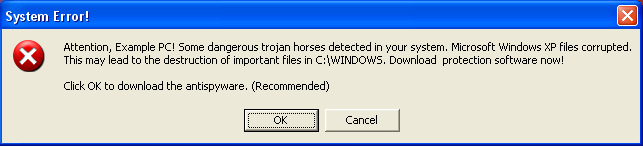
The wife of reader Chris came across the ruse when she used his PC to check on her Hotmail account. Before she could get onto the website she was confronted by a pop-up message saying "Chris [surname], your computer is infected with a Trojan, you should download this spyware removal tool (recommended)" and giving a yes/no option.
"I immediately closed it and am now running a scan to see what is causing this, but what was more concerning, and the reason that I am writing this to you, is that the perp of this malware/spyware/phishing attack has managed to write a program which can check the name that windows is registered to, to make it appear genuine," Chris told El Reg.
"This seems a really scary prospect to me, and I am IT savvy, but imagine Mr or Miss Average JoeShmo presented with that."
The malicious behaviour is identical to the Fakeale Trojan first spotted by net security firm Sophos last week. Carole Theriault, senior security consultant at Sophos, explained that the malware takes the user's name from the registry in order to craft a tailored warning message.
Fakeale Trojan false alarm
Users who respond to the come-on are taken the the website of an outfit punting a rogue anti-malware product. They are then told that their PC is infected with malware - even if it is clean - in a bid to frighten them into buying a product identified by Sophos as IE Defender installer.
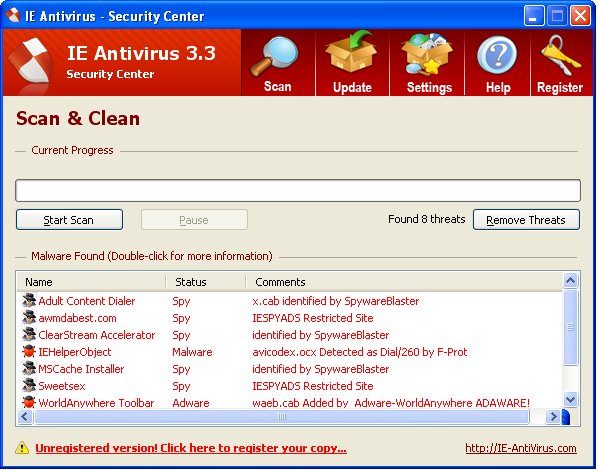
Goes down badly: results of the scan of a clean machine
Bogus warnings that attempt to trick users into purchasing "anti-malware tools" and have little or no security utility have been around for some time. The Paleale Trojan only differs in the use of trickery to make the unpalatable scam more convincing. ®
Bootnote
Thanks for Fraser Howard in Sophos Labs for the screenshots.
