This article is more than 1 year old
Vauxhall launches virtual backseat driver
Camera system warns of roadside signs
Vauxhall has developed an in-car safety system designed to alert drivers to roadside signs, or give them a ticking off when veering out of their lane.

Vauxhall's FCS lets you know when it spots a road sign
The Front Camera System (FCS) relies on a wide-angle camera positioned between the windscreen and rear-view mirror. The camera continuously snaps 30 pictures each second to scan the horizon for road signs and lane markings, at a distance of up to 100m.
FCS then picks out, say, speed signs by analysing the images for known roadsign shapes and detects numbers on the signs, such as 30mph, through colour comparison. Software’s then used to interpret the shapes and numbers, before a warning is sent to the driver.
For example, if FCS recognises a 30mph sign then it’ll display a warning on the car’s instrument panel to alert the driver that they’re approaching a 30mph speed zone.
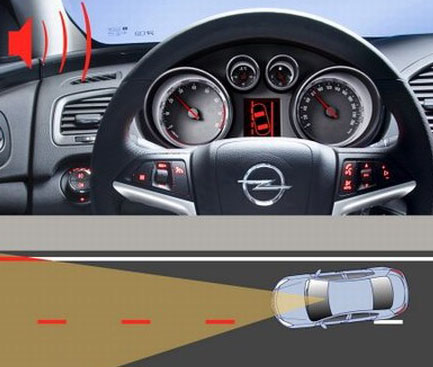
FCS also keeps you in-lane with visual and audible warnings
The system also recognises lane markings in much the same way. But, if a driver veers out of line then the virtual backseat driver gives off both a visual and an audible warning.
Vauxhall will introduce FCS as an optional extra on all new Insignia model cars.
But if engine noise reduction sounds more appealing to you, then you’ll be glad to hear that Toyota’s looking at ways to reduce the in-car noise on its hybrid vehicles.
The firm’s Active Noise Control uses three interior microphones to monitor in-car noise caused by the engine. Three speakers positioned around the inside of the car, including on the parcel shelf, then counteract the engine’s irritating noises by up to 8dB.
