This article is more than 1 year old
What hell hath science wrought lately?
A quick guide to man's abominations
In the beginning, things were simple. That's arguably because people were far more stupid, but let's not split hairs.
The point is, along came scientists with their fancy protractors, Bunsen burners and diesel-powered speedboats to complicate everything. Today there are scientific abominations all around us — and yes — they are coming to get you. (And we were hoping to keep this from you a bit longer, but they are also coming for your loved ones and family pet too.)
Seeing as how things move so quickly in this day in age, we thought it worthwhile compile a short list of some of things you need to worry about over the weekend.
Quoth Illidan: You are not prepared.
Chimeras
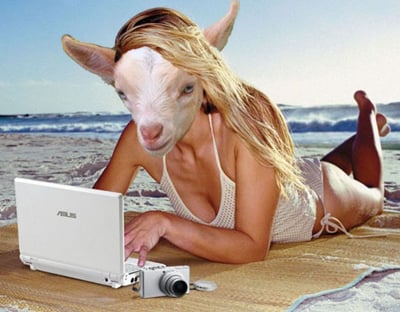
Science will ruin everything. Everything.
Scientists at the University of Nevada say they've figured out how make a human-sheep chimera. That's a sheep with 85 per cent animal cells and 15 per cent human cells.
It's done by an elegant process of sucking stem cells out from a person's bone marrow and injecting them into the unripe belly of a sheep fetus. The apparent point is to one day let animals rather courteously grow our organs for human transplant.
Here's the deal — the only place where human bone marrow and sheep fetuses should be mixed together is the grinder in a hotdog factory. And sheepmen? Really? We'll bet a good portion of our readers have turned off the filtering on Google Image Search and accidentally seen drawings of what some people fantasize doing to human/animal hybrid creatures. (And Mrs. Buttersworth too, apparently. I still have nightmares.)
If all that's not enough to scare you, this author has a handy little reference manual called a "D&D sourcebook" and it flat-out says Chimera are by nature chaotic evil. And 2d6+4 bite attacks aren't something our children should be exposed to. Ever.
Call me old fashion.
But back to the organ thing. A lot of us sleep better knowing, worst comes to worst, there's a guy that knows a guy who will pay a lot of money for a human kidney — no questions asked. Suddenly Joe Renal Disease can upgrade to an A-grade sheep organ for a song. Where does that leave us growing organs au naturel? These creatures are coming for our rent money too.
Danger level: 3/5
