This article is more than 1 year old
IBM fills chips with water
Beating the 3-D stacking heat
Oh, those crazy kids at IBM's Zürich lab. They can't get enough of processor cooling technology.
Two years ago, IBM announced a breakthrough with carving channels into chips to let thermal paste sink down nearer the silicon. Then, in 2007, IBM Zürich patted itself on the back for cutting more channels into the cooling unit. Now, IBM looks to pump water between stacks of processors and other common motherboard components to keep them cool.
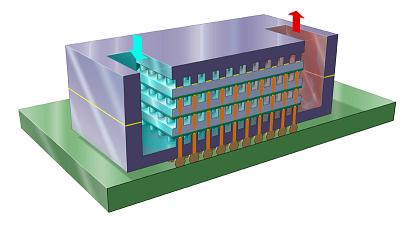
The chip industry has become rather enamored with the idea of 3-D stacking where processors and memory, among other things, sit right on top of each other instead of near each other on a motherboard. This should help increase the speed at which data flows between the various components by opening up many more communications paths. By shrinking wires to about 1/1000th of their usual size, chip makers can also help reduce the energy consumption of their products.
But, while there are overall energy consumption benefits, chip engineers must still battle with removing heat from the processor - a struggle made worse when you cram lots of hot stuff together.
"3-D chip stacks would have an aggregated heat dissipation of close to 1 kilowatt - 10 times greater than the heat generated by a hotplate - with an area of 4 square centimeters and a thickness of about 1 millimeter," IBM said. "Moreover, each layer poses an additional barrier to heat removal."
To deal with the heat, IBM has discovered a way to pipe water into cooling tunnels that are about as thin as a human hair and that sit in between die layers of a processor. The cooling layer between the die layers comes in at about 100 microns and contains about 10,000 vertical interconnects per cm2 between the layers.
All told, the IBM scientists showed cooling of "up to 180 W/cm2 per layer for a stack with a typical footprint of 4 cm2."
IBM's Cool Pipes
The IBM researchers told us that the technology will still be years away from production and whether it gets used or not will depend on how chip makers end up approaching 3-D stacking. That said, IBM can play off existing chip manufacturing techniques to get most of the way to the water-filled chips. "The only additional process is that of bonding the layers together," IBM told us. ®
