This article is more than 1 year old
NASA bites nails over Phoenix landing
Lander's Red Planet encounter looms
NASA's Phoenix Mars Lander is on its final approach for a slated touch-down on the Red Planet's Arctic region on 25 May amid a certain amount of nail-biting as to whether it will survive the landing.
Ed Weiler, associate administrator for NASA's Science Mission Directorate, admitted yesterday: "This is not a trip to grandma's house. Putting a spacecraft safely on Mars is hard and risky. Internationally, fewer than half the attempts have succeeded."
The biggest threats to the spacecraft are rocks "large enough to spoil the landing or prevent opening of the solar panels". However, Ray Arvidson of Washington University in St Louis, chairman of the Phoenix landing-site working group, assured: "We have blanketed nearly the entire landing area with HiRISE images. This is one of the least rocky areas on all of Mars and we are confident that rocks will not detrimentally impact the ability of Phoenix to land safely."
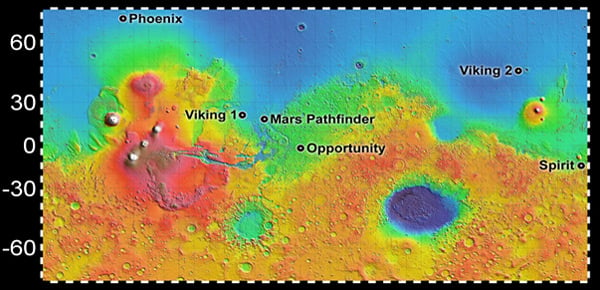
NASA has released a map showing where Phoenix is scheduled to make contact with the Martian surface, which at around 68° north is further into the Red Planet's Arctic zone than previous missions have ventured:
Phoenix will enter the top of the Martian atmosphere at a tad under 13,000mph (21,000km/h) and has just seven minutes to complete a "challenging sequence of events" - using "heat-generating atmospheric friction, then a parachute, then firings of descent thrusters" which will slow it to 5mph (8km/h) for landing on its three legs.
All being well, the intact lander will then be able to get down to the business in hand and "study the history of water in the Martian arctic" and "search for evidence of a habitable zone and assess the biological potential of the ice-soil boundary".
To achieve these two "bold objectives", Phoenix will deploy its arsenal of instruments: Surface Stereo Imager; Robotic Arm Camera; Mars Descent Imager; Thermal and Evolved Gas Analyzer; Microscopy, Electrochemistry, and Conductivity Analyser; Wet Chemistry Experiment; Microscopy, including the Optical Microscope and the Atomic Force Microscope; Thermal and Electrical Conductivity Probe; and Meteorological Station.
The University of Arizona has more on the mission's science here. ®