This article is more than 1 year old
Interpol appeal unmasks US actor as child abuse suspect
Operation IDent-ification
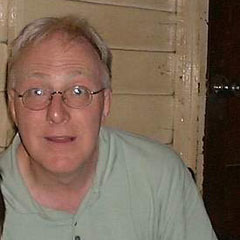
A man matching the description of a suspected child abuser who became the target of an international manhunt earlier this week has been arrested in the US.
Wayne Nelson Corliss, 58, was arrested in Union City, New Jersey on Thursday - two days after Interpol published photos resembling him. The actor, whose stage name is Casey Wane, is suspected of sexually abusing at least three boys aged between six and ten in south east Asia between April 2000 and May 2001.
Interpol Secretary General Ronald Noble hailed Corliss's arrest: “Two days ago, this man’s nationality, identity and location were totally unknown. All we had to go by were a series of graphic photographs in which the suspect was seen sexually abusing young children and our confidence that the public and police worldwide would once again respond... That two days later, the primary suspect is now in custody is an outstanding achievement and a credit to the citizens, media and law enforcement worldwide who responded to Interpol’s call.”
In March 2006, police in Norwary found images of the abuse on the PC of a convicted paedophile. Two years of police investigation failed to identify the grey-haired, bespectacled suspect, or even his nationality. This prompted Interpol to publish six pictures of the man on Tuesday, in only its second appeal to find a suspected paedophile.
Last year a similar appeal uncovered the identity of Canadian Christopher Paul Neil, who is in jail awaiting trial on child abuse charges. German police unscrambled an image of Neil's face that had been "swirled" to hide his identity. The picture was contained in a cache of child abuse images, and its publication by Interpol last October quickly led to his arrest in Thailand.
More from Interpol here. ®
