This article is more than 1 year old
Cash, blow-up dolls and mime artist star at spyware knees-up
Cybercrims launch Bacchanalia 2.0
NSFW It's common knowledge that malware has become the purview of cybercriminals rather than mere mischief-makers. But unlike the frolics of dotcom yuppies, the excesses of Eastern European cybercrooks have rarely been chronicled.
So, we're indebted to the upstanding affiliates of Klik Revenue, a Russian-based outfit that allegedly pushes (pdf) rogue anti-spyware apps and games search engines, among other miscellaneous activities, for documenting their latest party. Held in the Bianca Resort Hotel SPA in Montenegro in February, the event featured wads of cash in briefcases, flash cars, plenty of booze and inflatable love dolls. And, inexplicably, a mime artist.
The lads have chronicled their work on YouTube (below). A range of pictures can be found here. And in the true spirit of Web 2.0, there's more on this blog.
This year's event is a village fete compared to Klik's previous party in Prague two years ago, which boasted strippers dressed as FBI agents and other X-rated excesses.

As Sunbelt Software notes: "It's good to see that these nice, upstanding boys are having so much fun with their honest, hard-earned money."
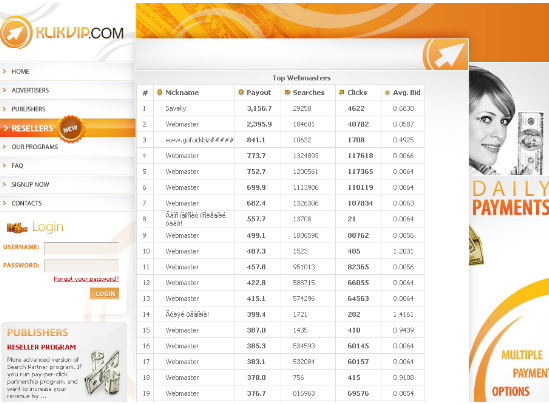
The Klik gig was drawn to our attention in a presentation by Panda Security, at a recent event in Barcelona. A screenshot of Klik's internal stats engine, obtained by Panda, can be found below.
Russian anti-virus firm Kaspersky Labs said that Klik's business is illegal under Russian law, pointing out the difficulties of cybercrime prosecutions that can leave suspected crooks (in Russian and elsewhere) uncuffed.
Yuri Mashevsky, senior virus analyst at Russian net security firm Kaspersky Lab, said: “Unfortunately, the Klik group is just one of many such groups operating in Russia, and so far such organizations feel relatively safe. Their actions span not only fake anti-spyware, abuse-proof hosting services, but also a huge number of fake online-shops (which receive money from customers but send them nothing in return). Such groups also trade malware, which is often custom-tailored for their 'clients' needs. As a result, the amount of money earned by such criminal groups is stunning."
The Klik group's activities are illegal under Russian law, and punishments can be severe. "However, like their colleagues in other countries throughout the world, due to many reasons Russian legal authorities have a lot of trouble investigating such crimes and proving the guilt of cybercriminals," Mashevsky explained.
"First of all, to start an investigation they need a legal application from the victim, and in the majority of cases there are no such applications. Besides, modern cybercriminals are rather professional people, and they know how to hide their tracks.
"Hence, such cases rarely make it to the court. But sometimes Russian legal authorities crack some very complicated cases, like the one when in December 2007 Russian FSB managed to find and arrest the authors of the notorious 'Pinch' Trojans, which are one of the most widespread pieces of crimeware."
Klik Revenue doesn't publish contact numbers on its website. Our attempts to reach it by email failed when messages bounced from support and business development mailboxes were said to be full. ®
